15 April 2026 • Wireshark & Nmap Analysis
Network Traffic Analysis Report v3.0
ANALYST
Youssef Moataz
ENVIRONMENT
Kali Linux (VMware NAT)
DURATION
~12 Minutes
1. Executive Summary
This report documents a technical analysis of network traffic captured during a simulated cyber attack. The study focused on baseline behavioral mapping and reconnaissance detection.
Patterns identified include high-volume SYN scanning, unencrypted data exchange, and service discovery on the local gateway. The findings highlight the importance of network visibility in identifying adversarial behavior early in the attack lifecycle.
2. Methodology & Timeline
Goals
- Analyze packet-level traffic flow.
- Differentiate between normal and suspicious patterns.
- Model attacker behavior using Nmap.
- Identify security gaps in local services.
Analysis Phases
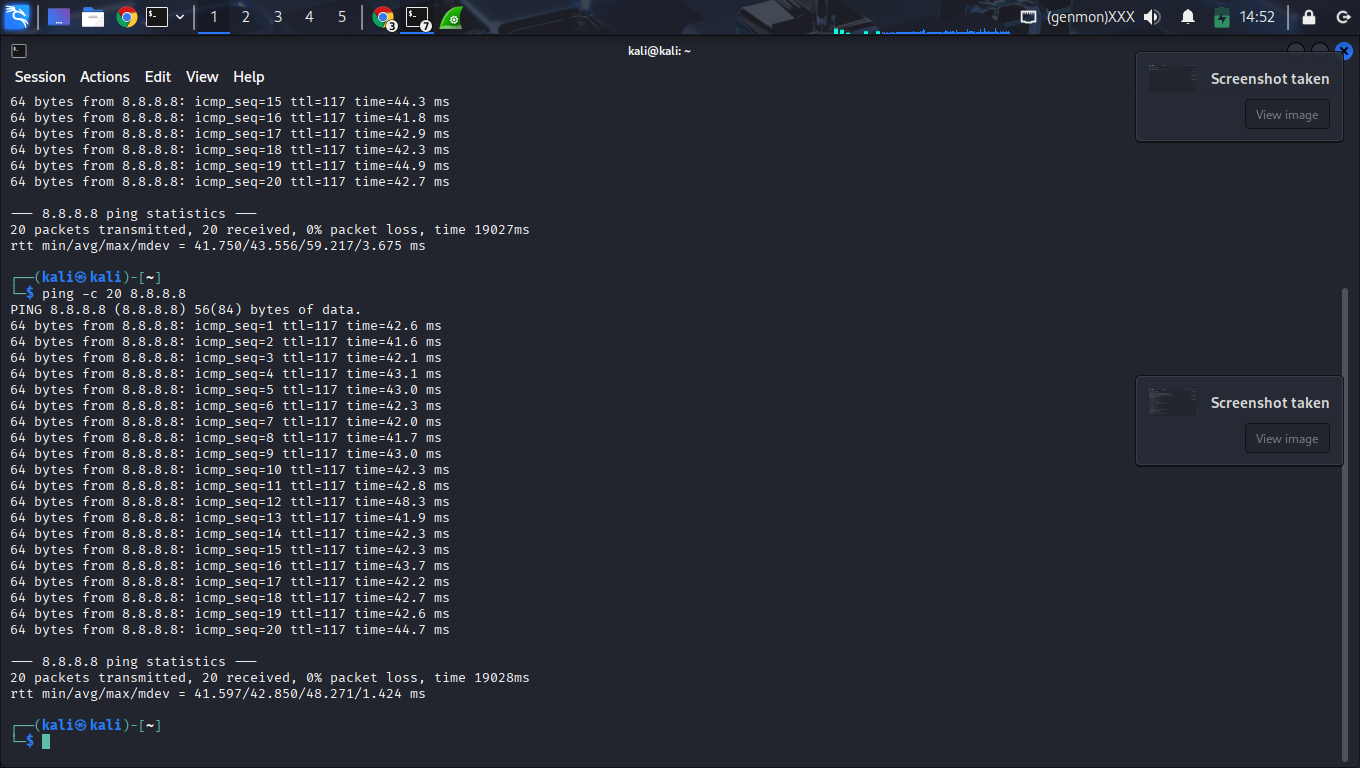
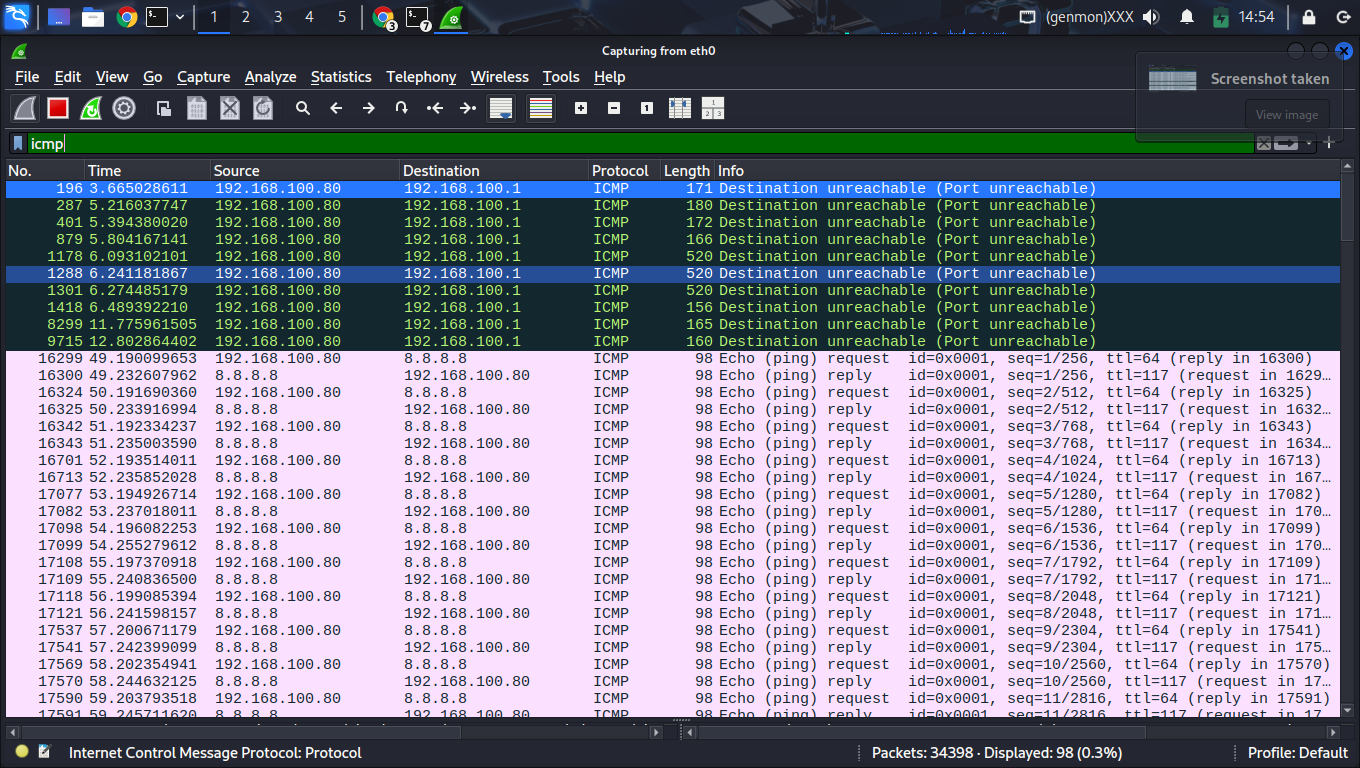
4-6m: ICMP Reachability Checks
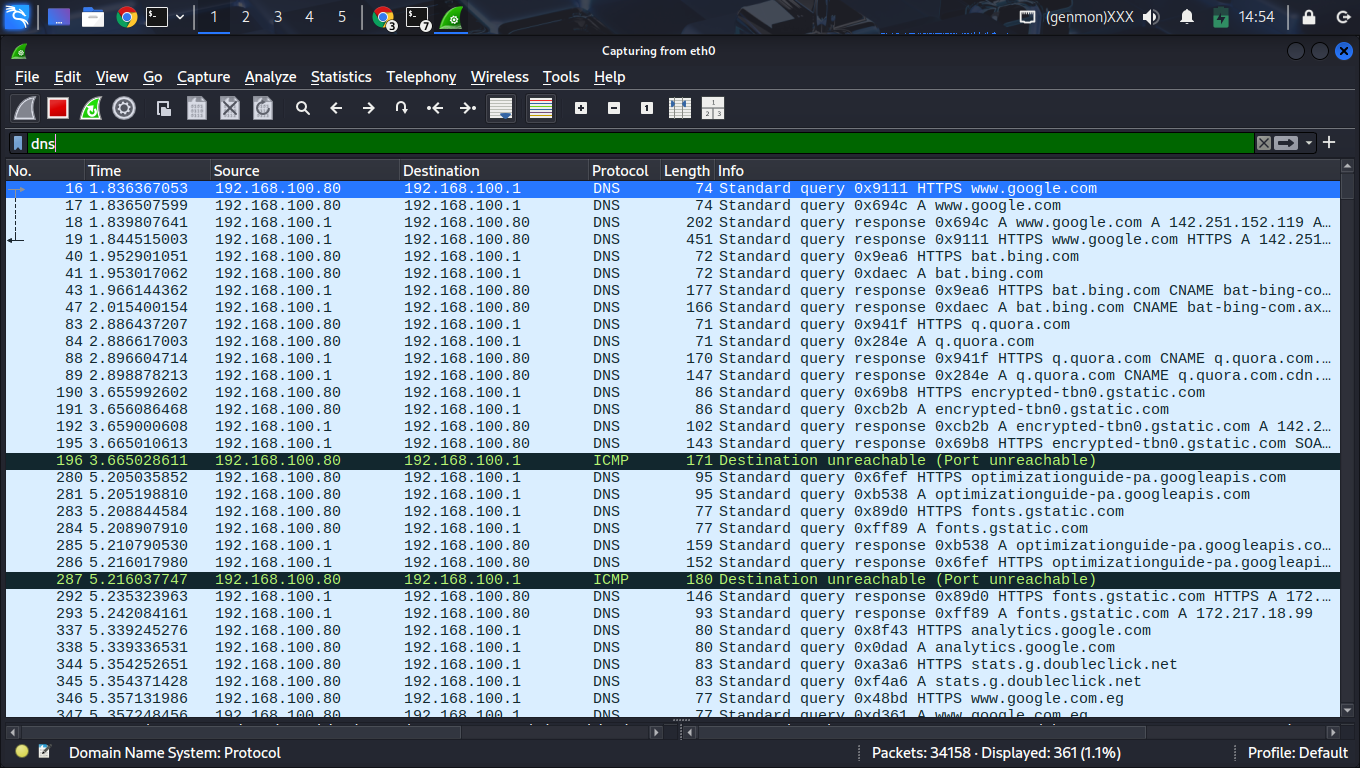
6-9m: Reconnaissance (SYN Scan)
9-12m: Service Enumeration (HTTP)
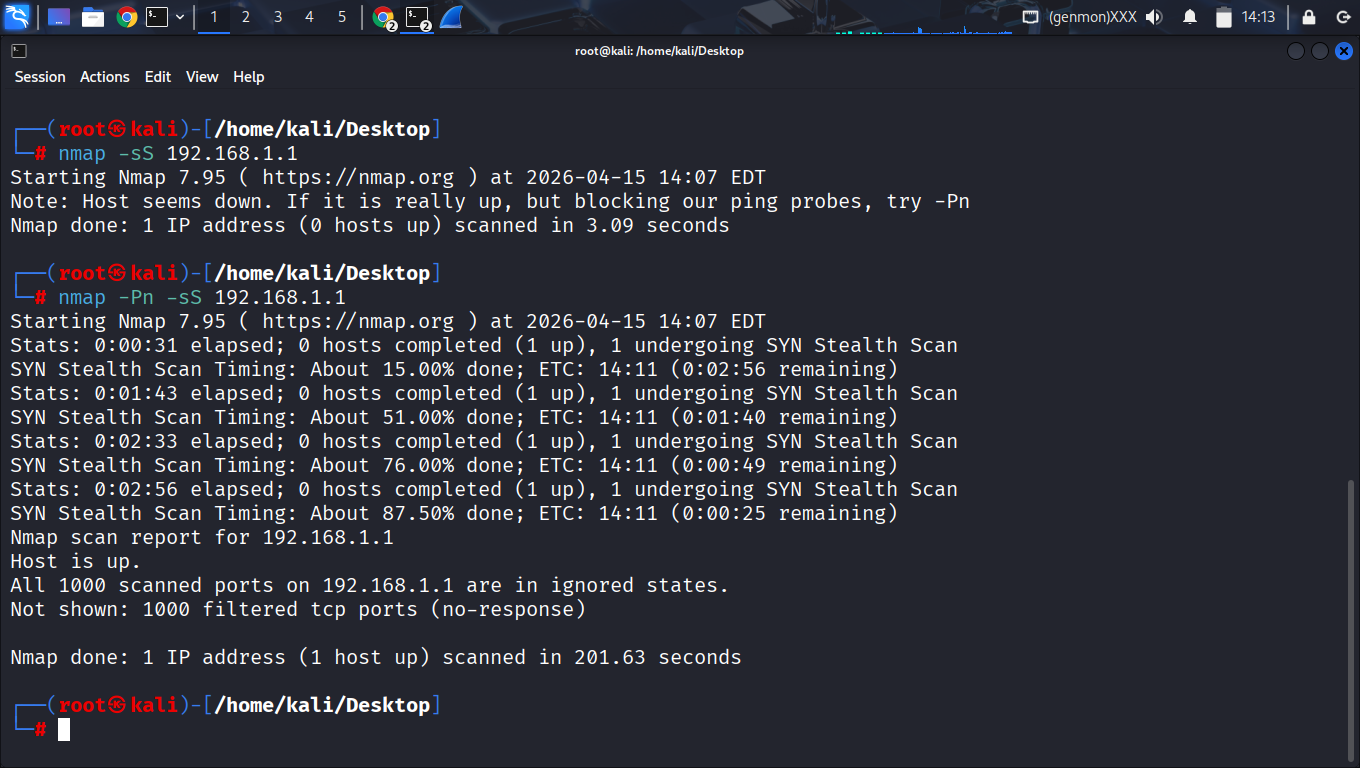
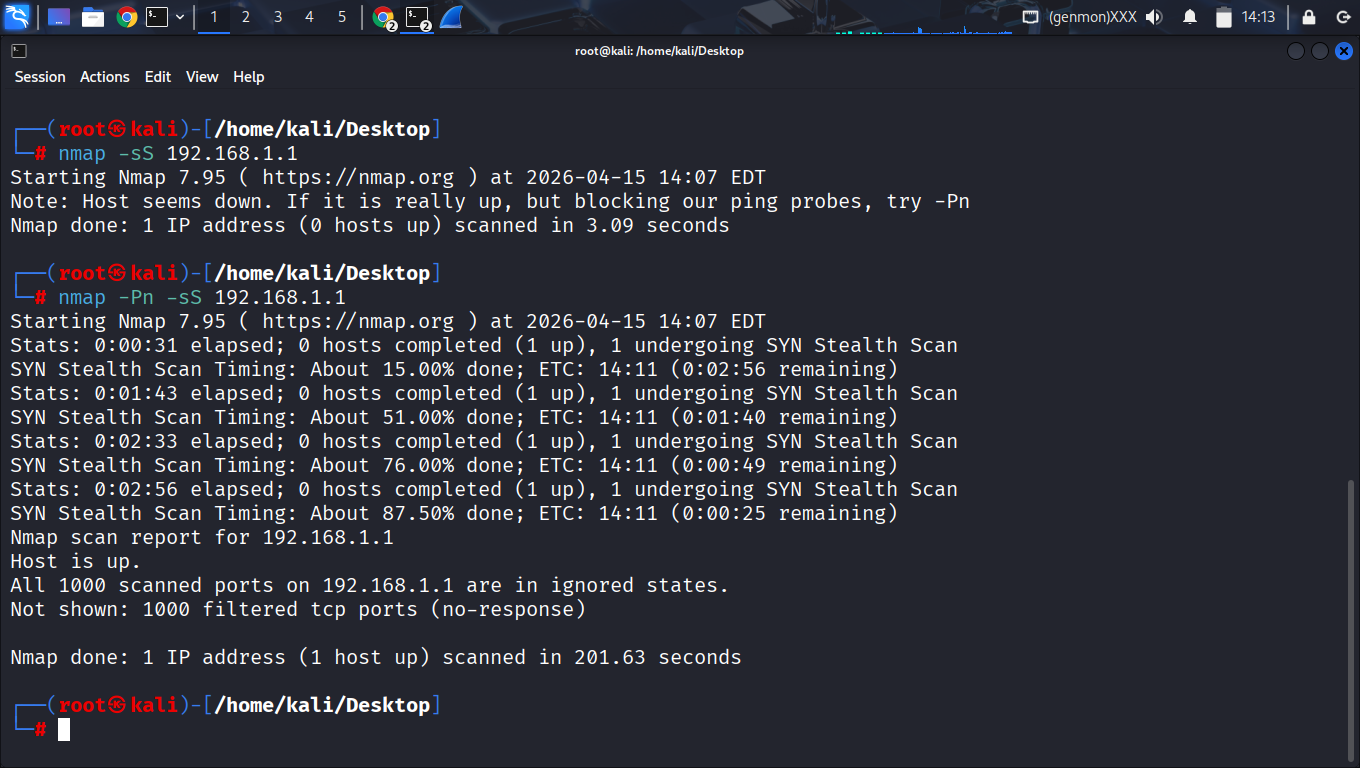
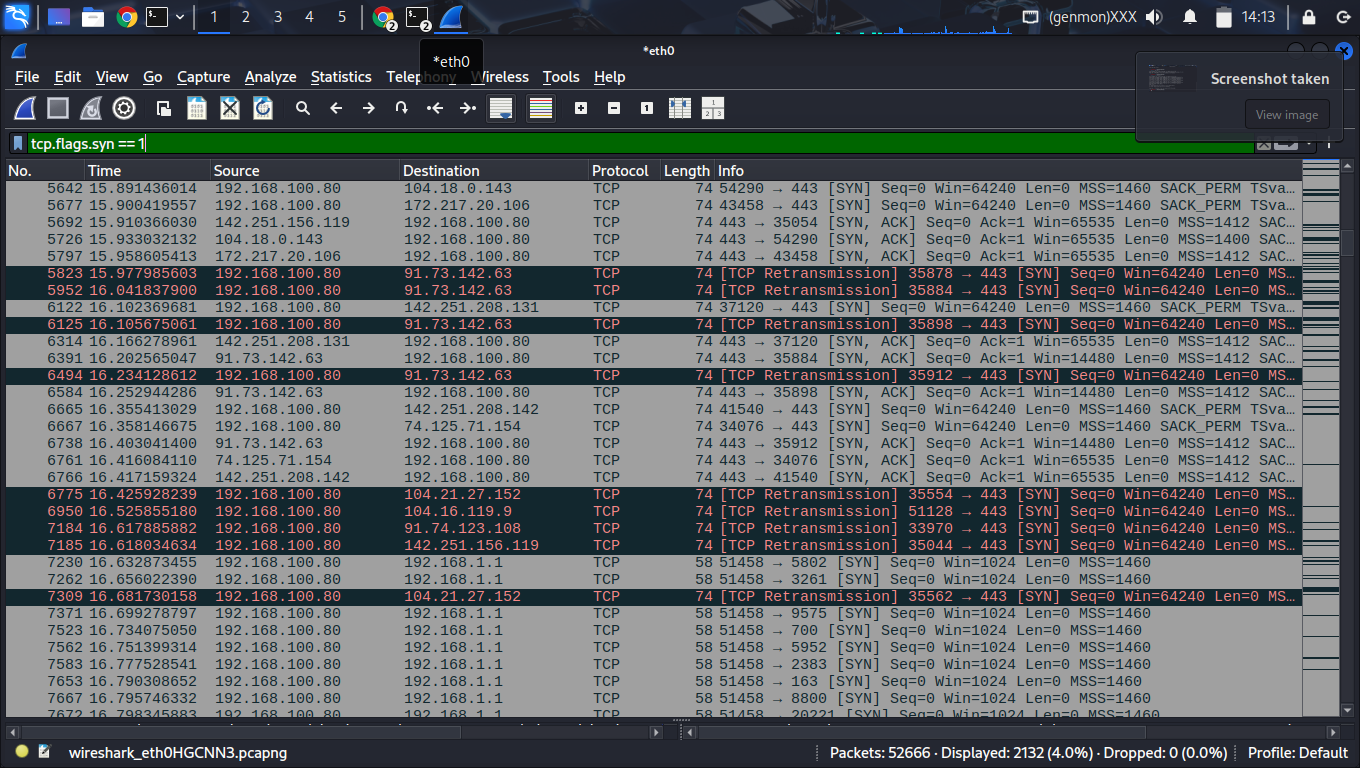
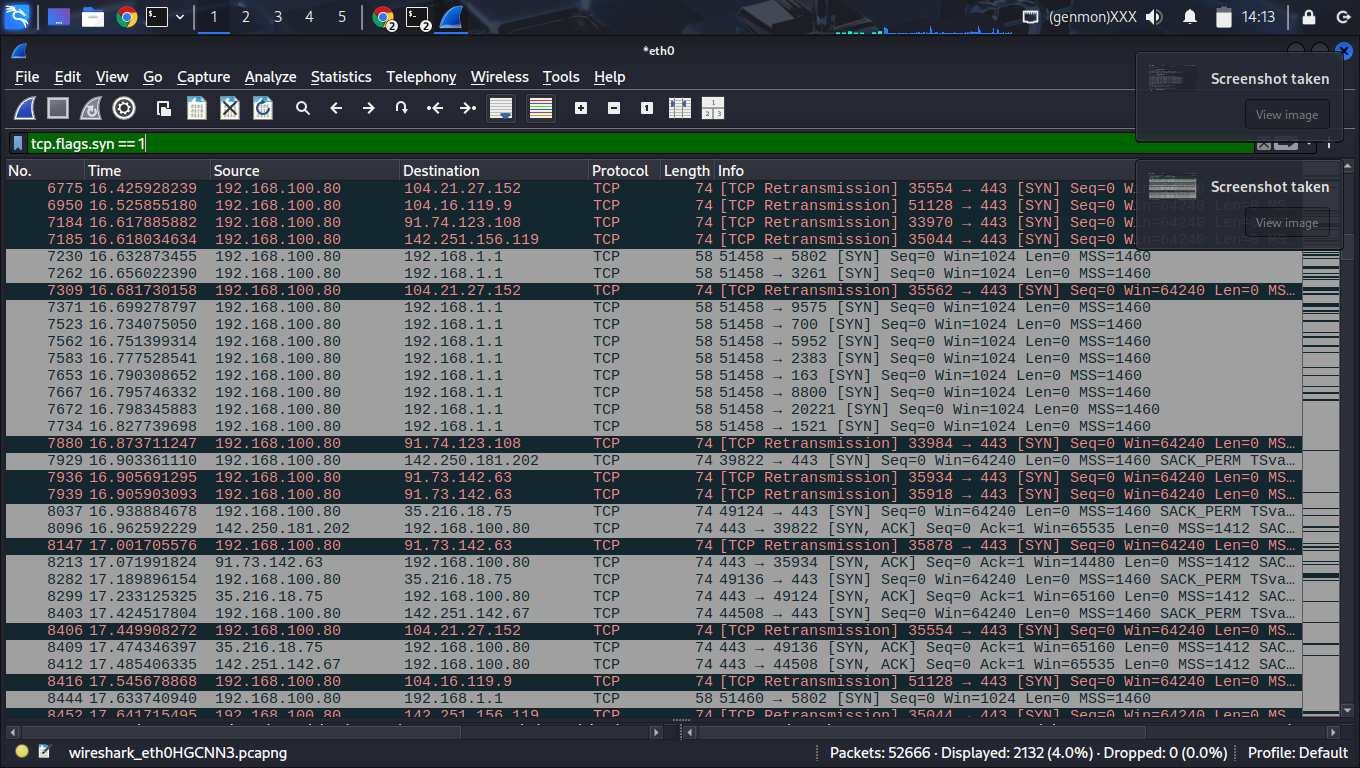
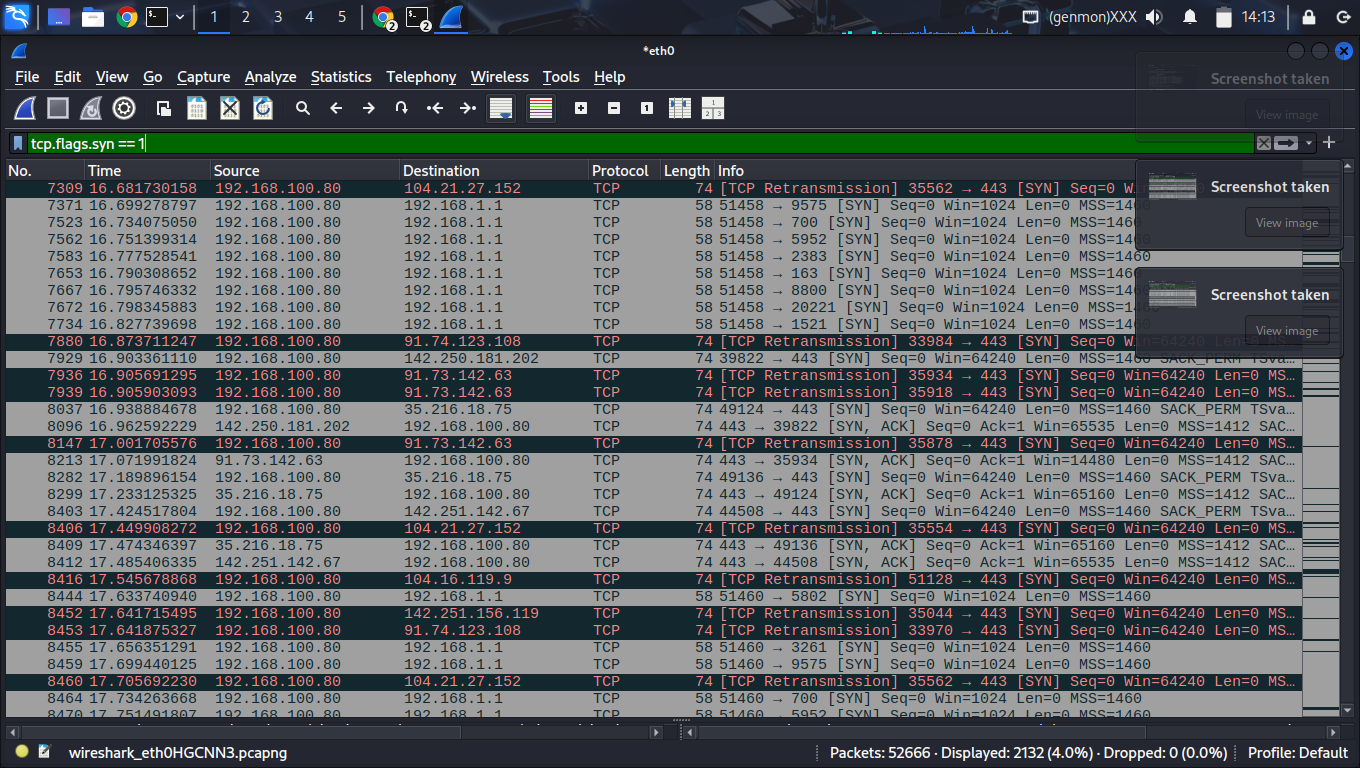
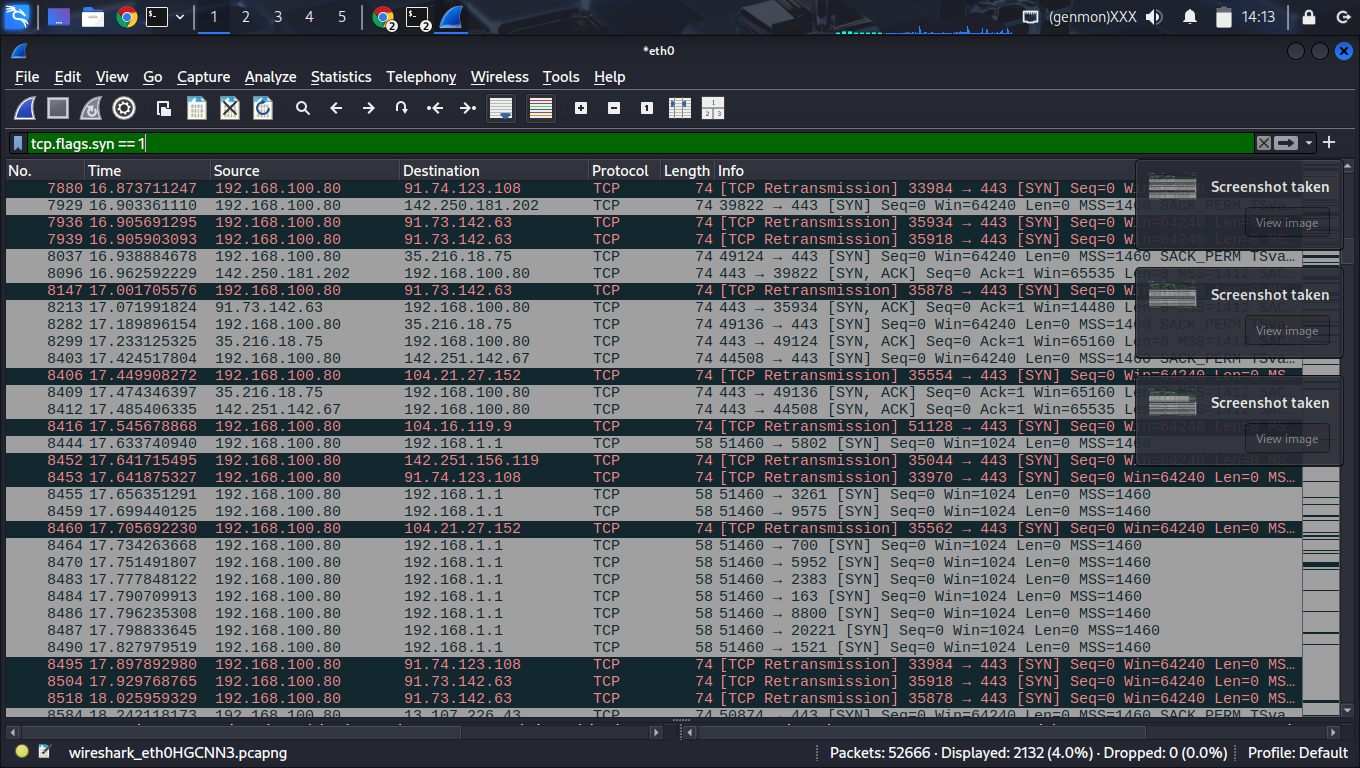
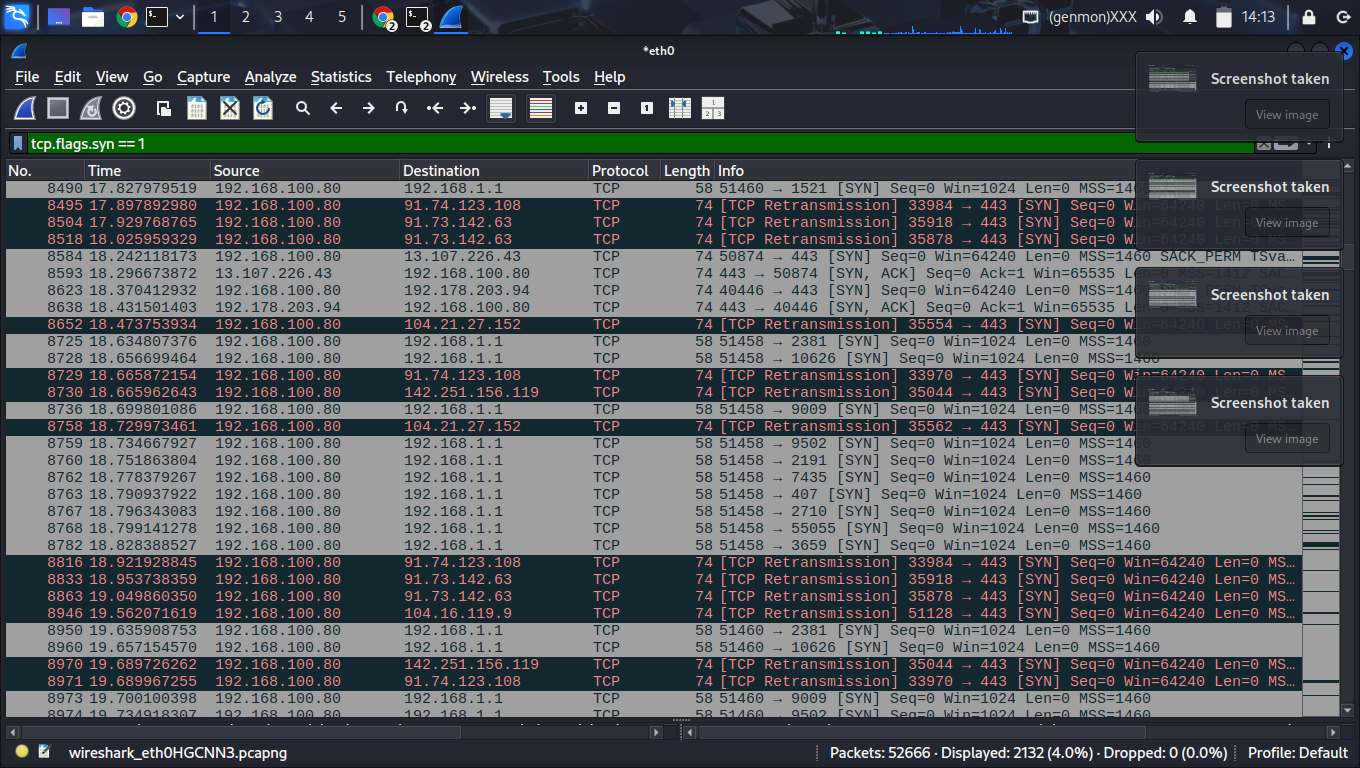
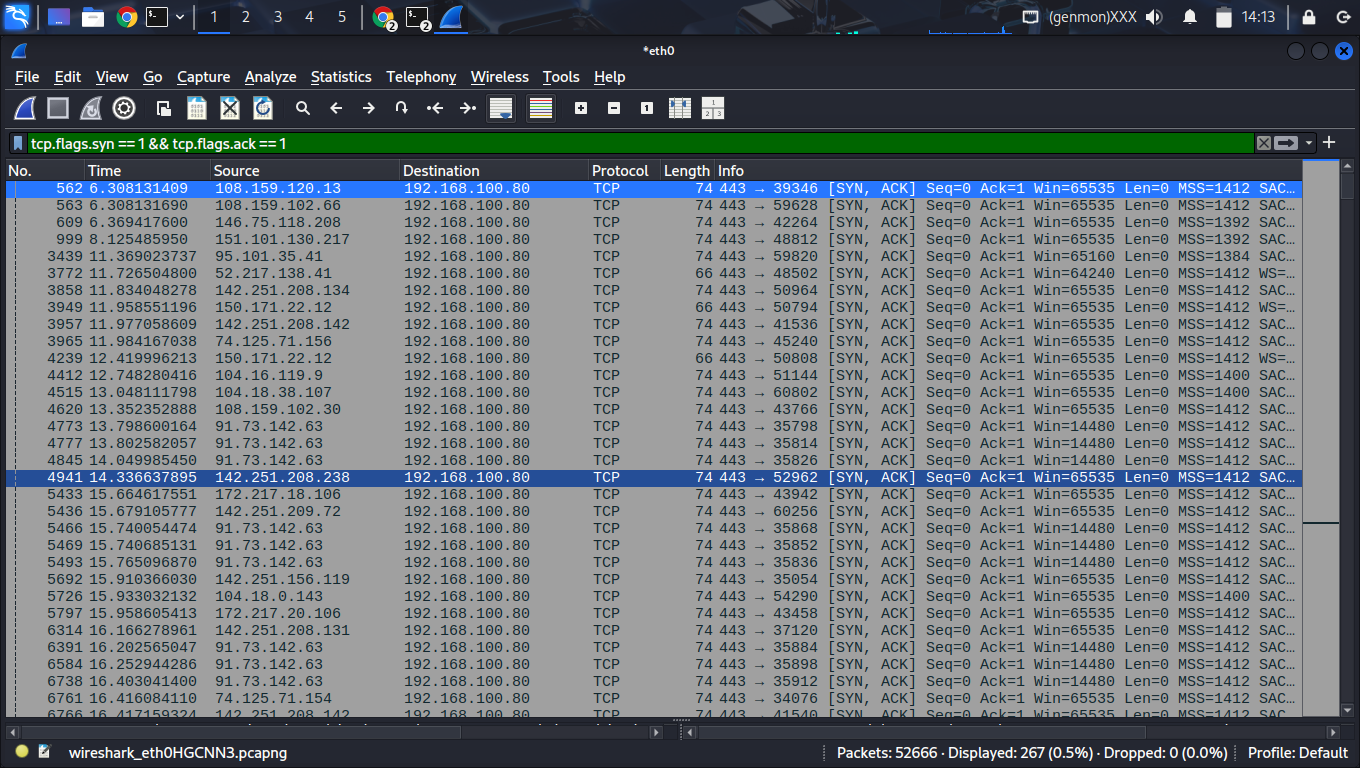
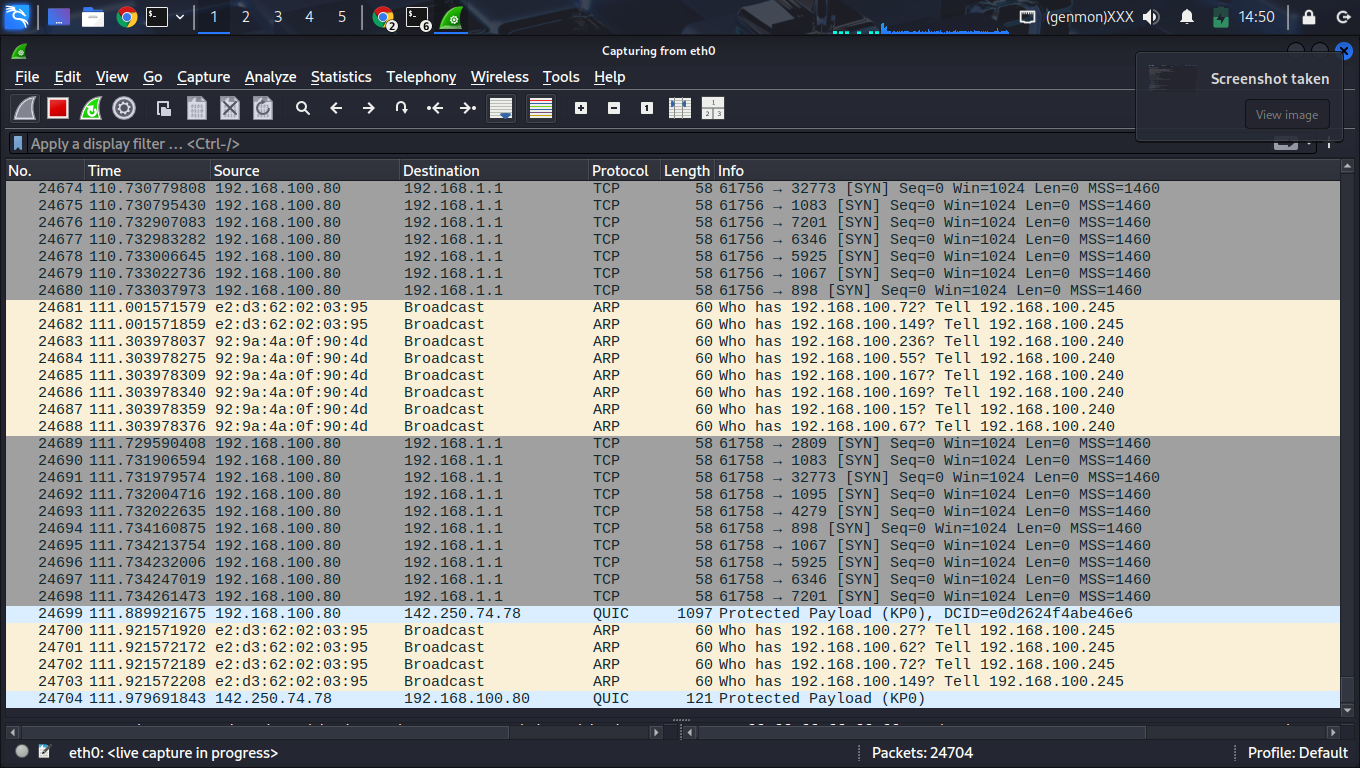
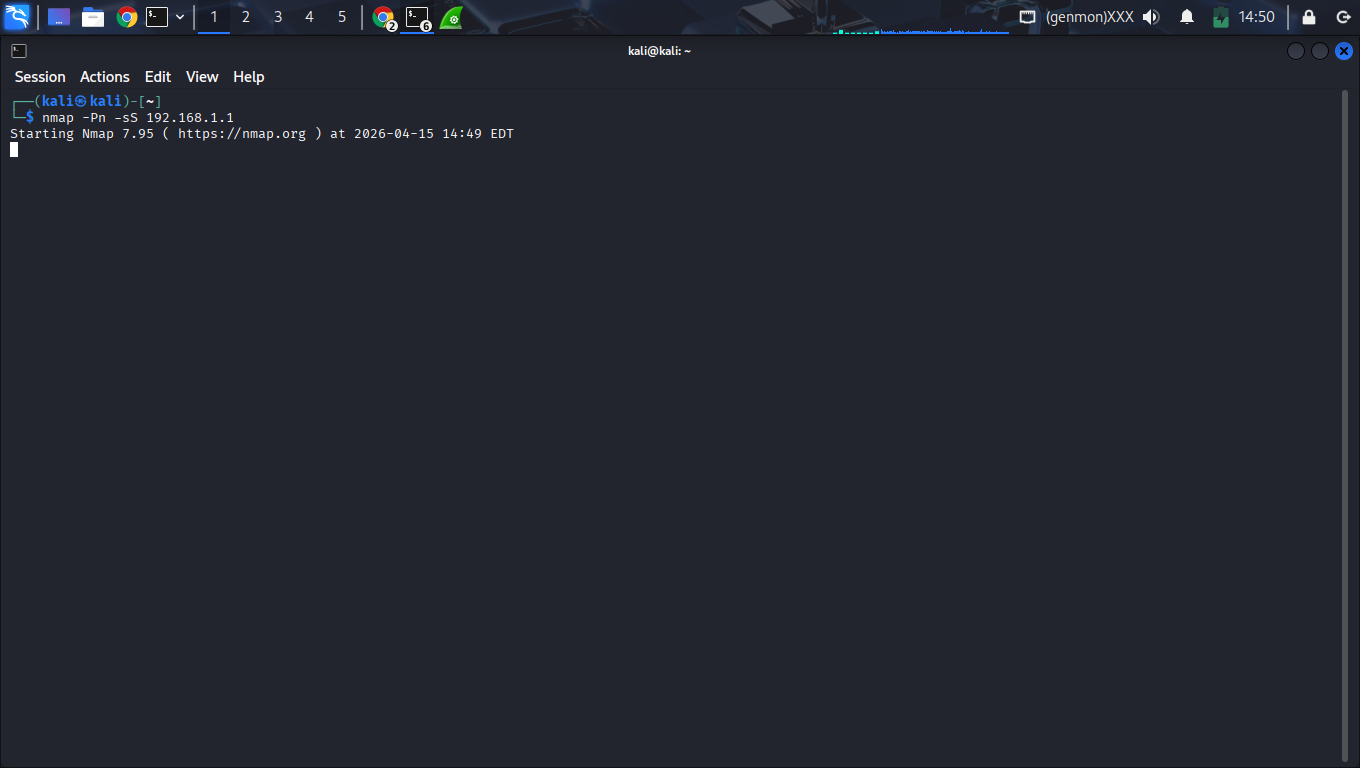
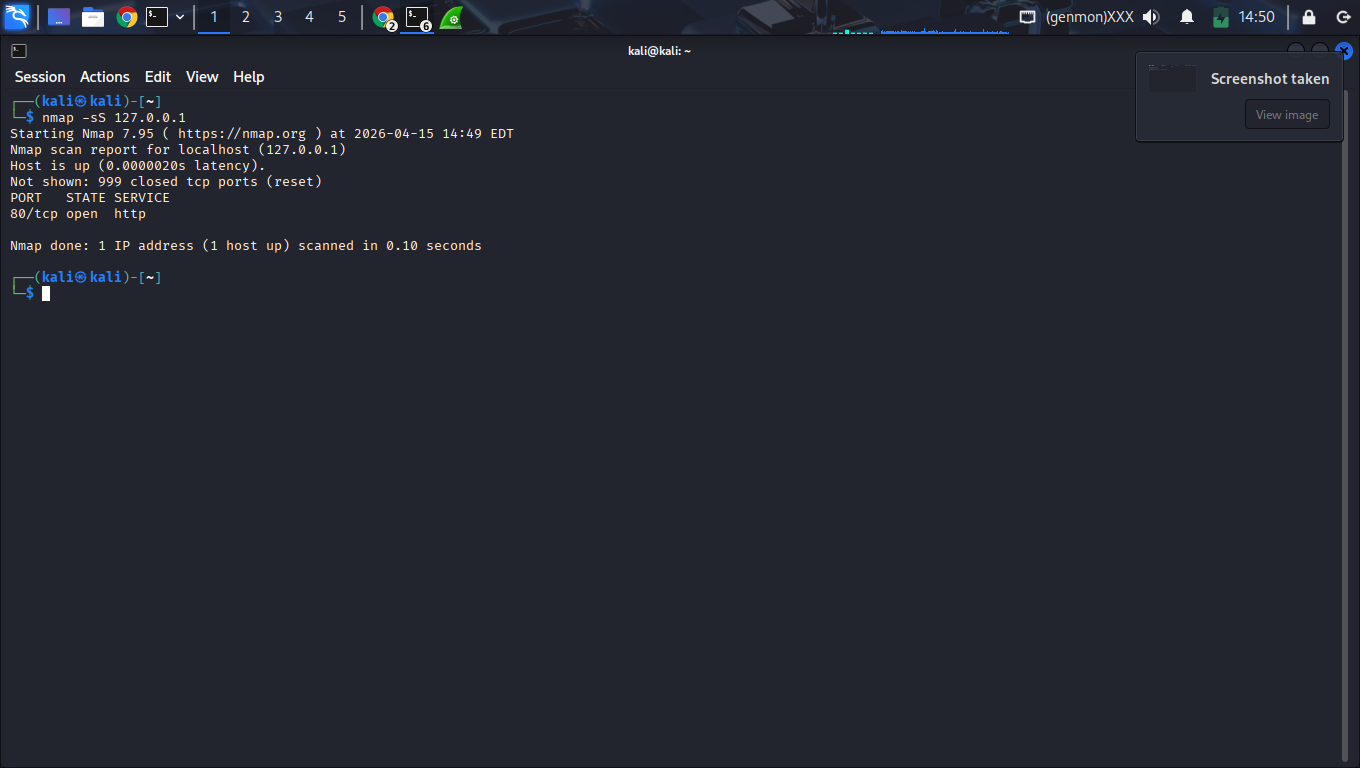
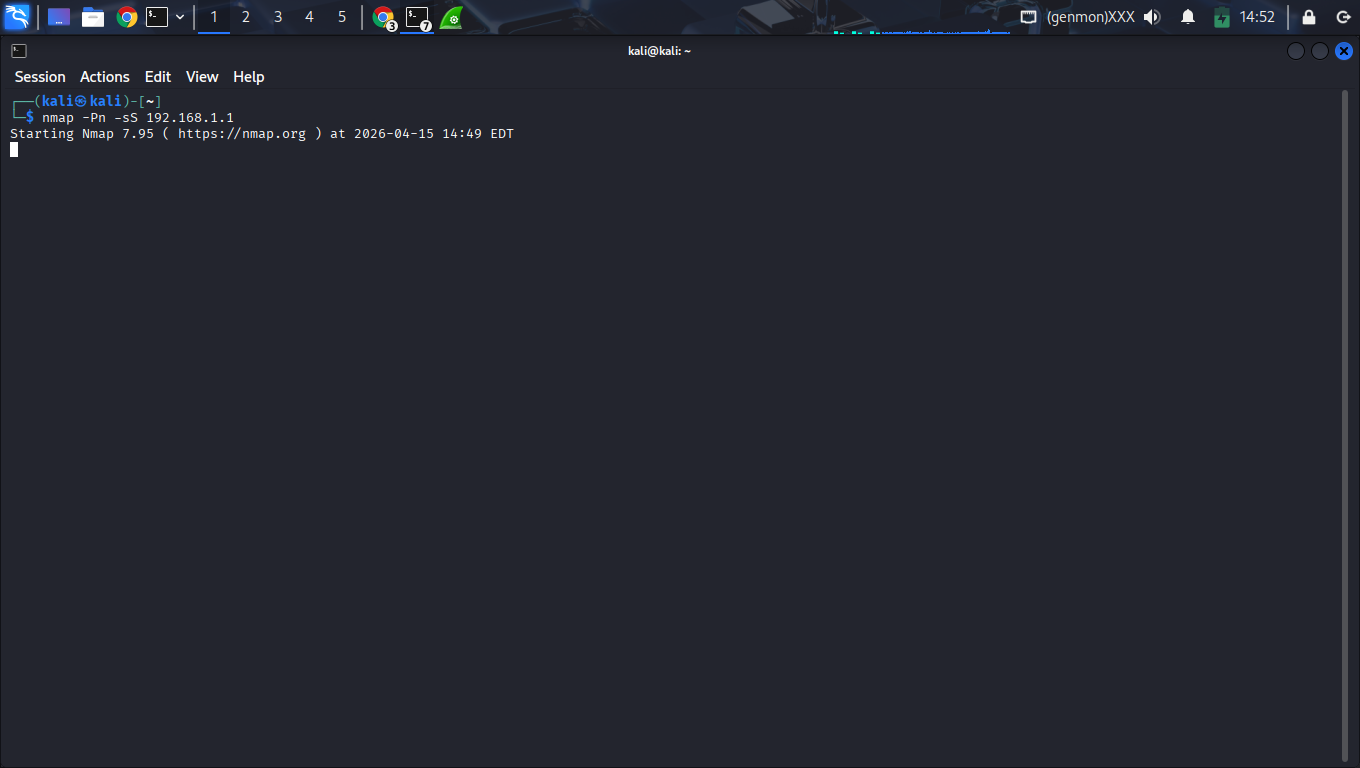
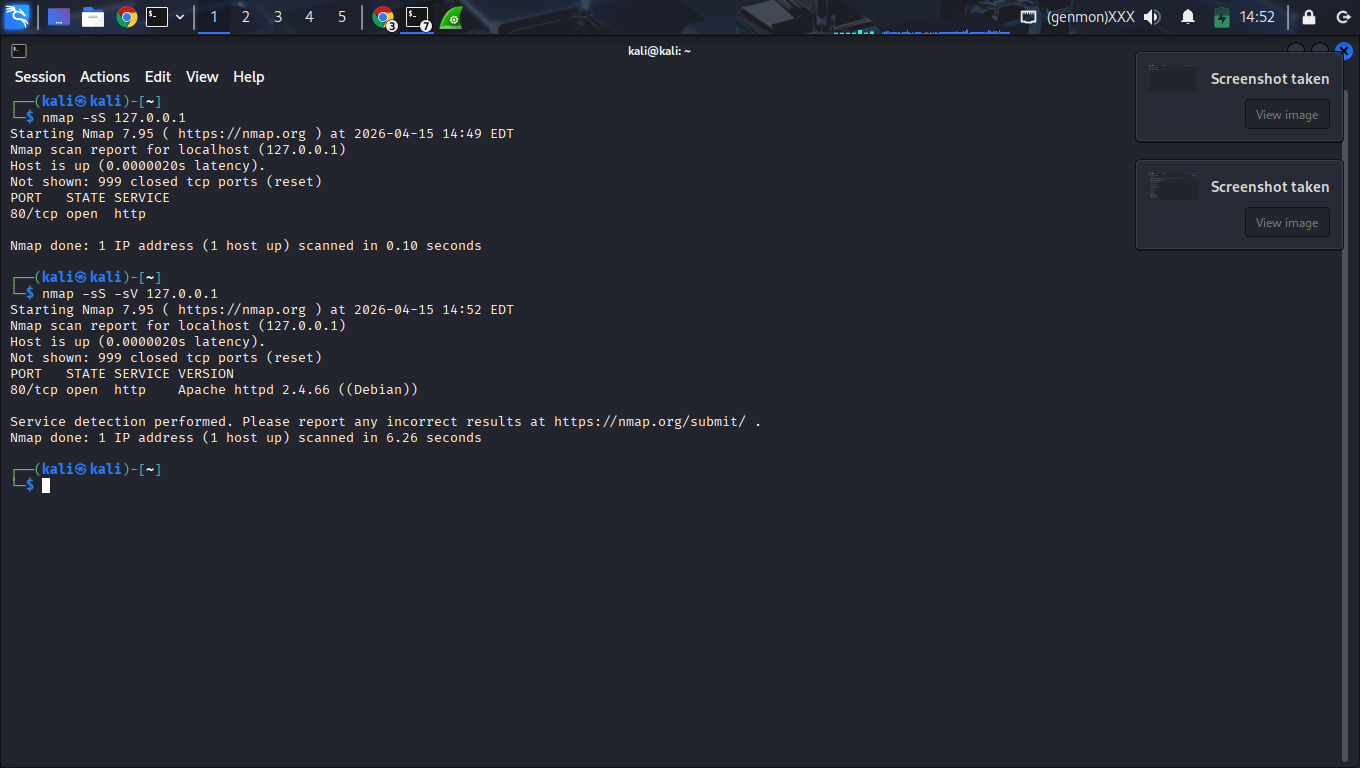
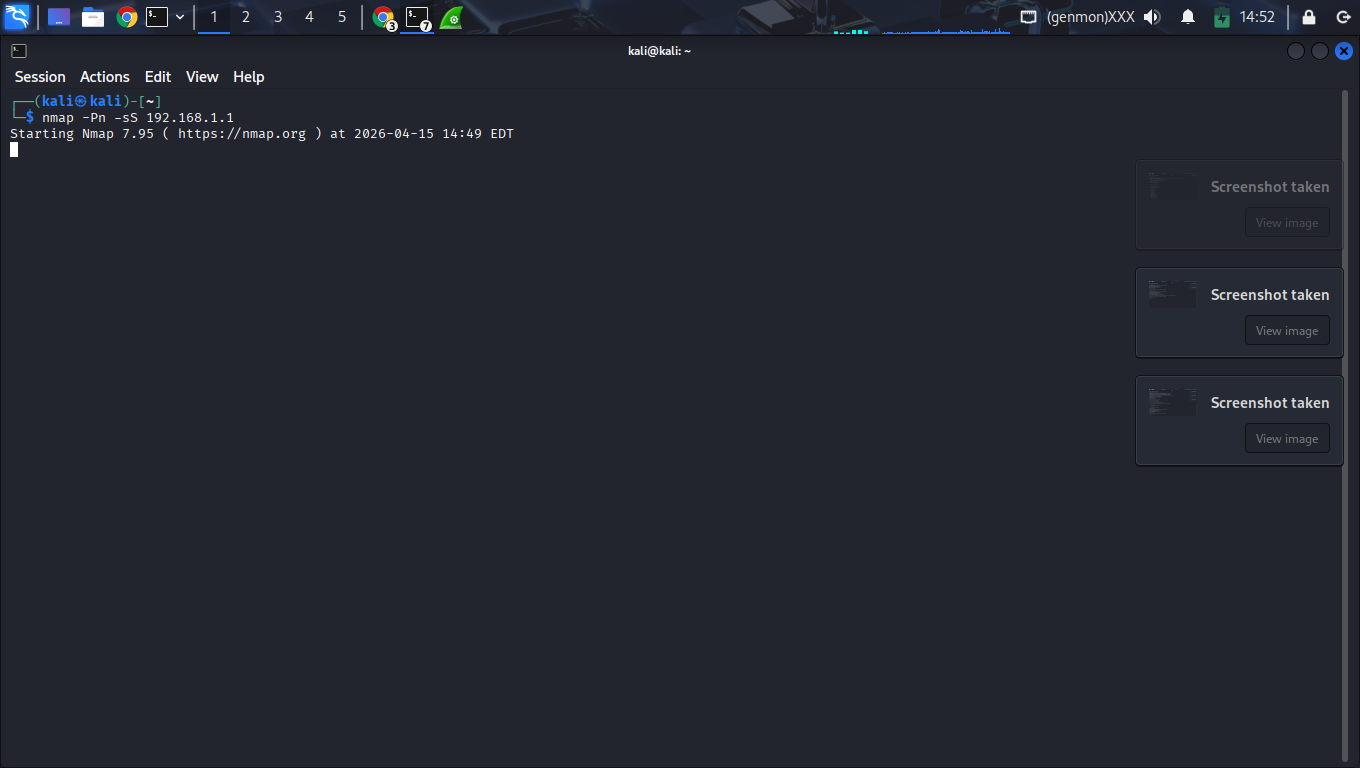
3. Reconnaissance: Stealth SYN Scan
High SeverityTechnical Indicators
Source: Kali VM
Target Gateway: 192.168.1.1
Activity: ~1.3k SYN packets
Wireshark Search
tcp.flags.syn==1 && tcp.flags.ack==0
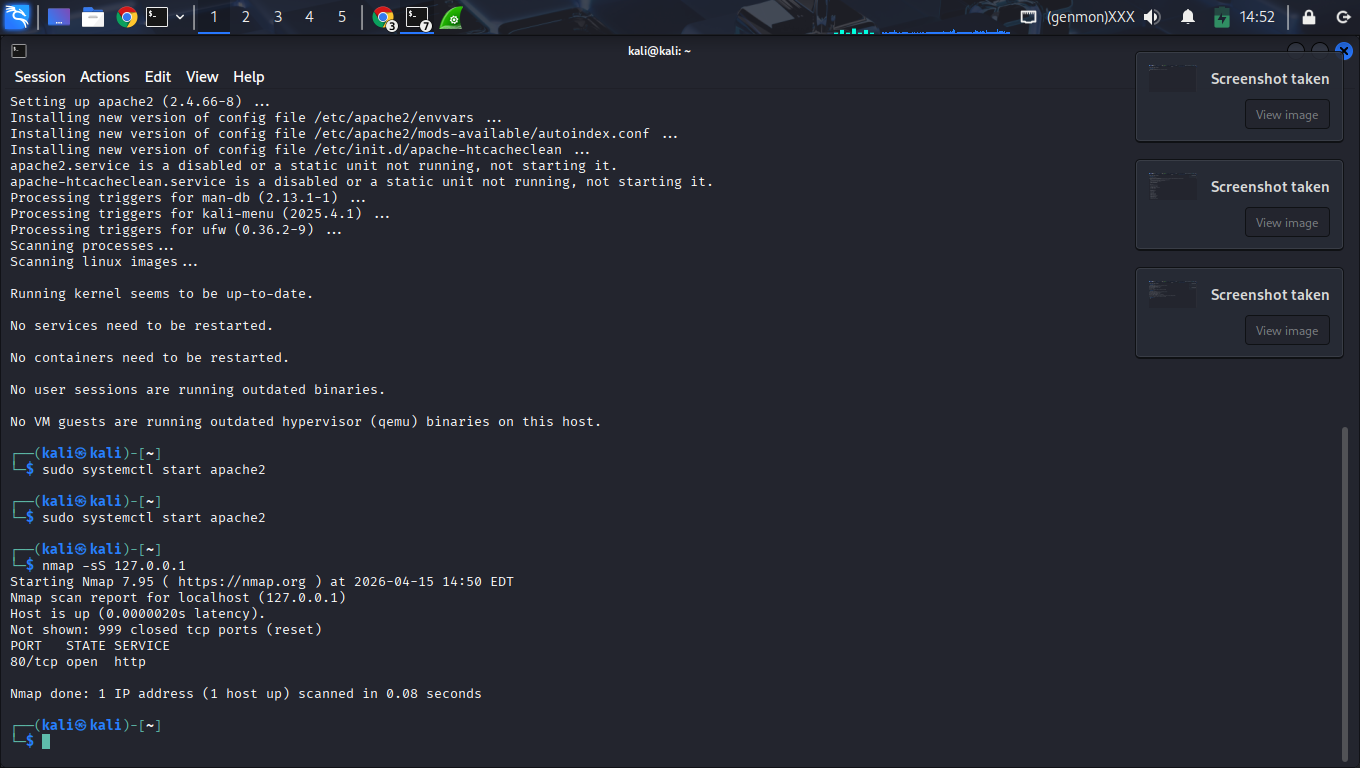
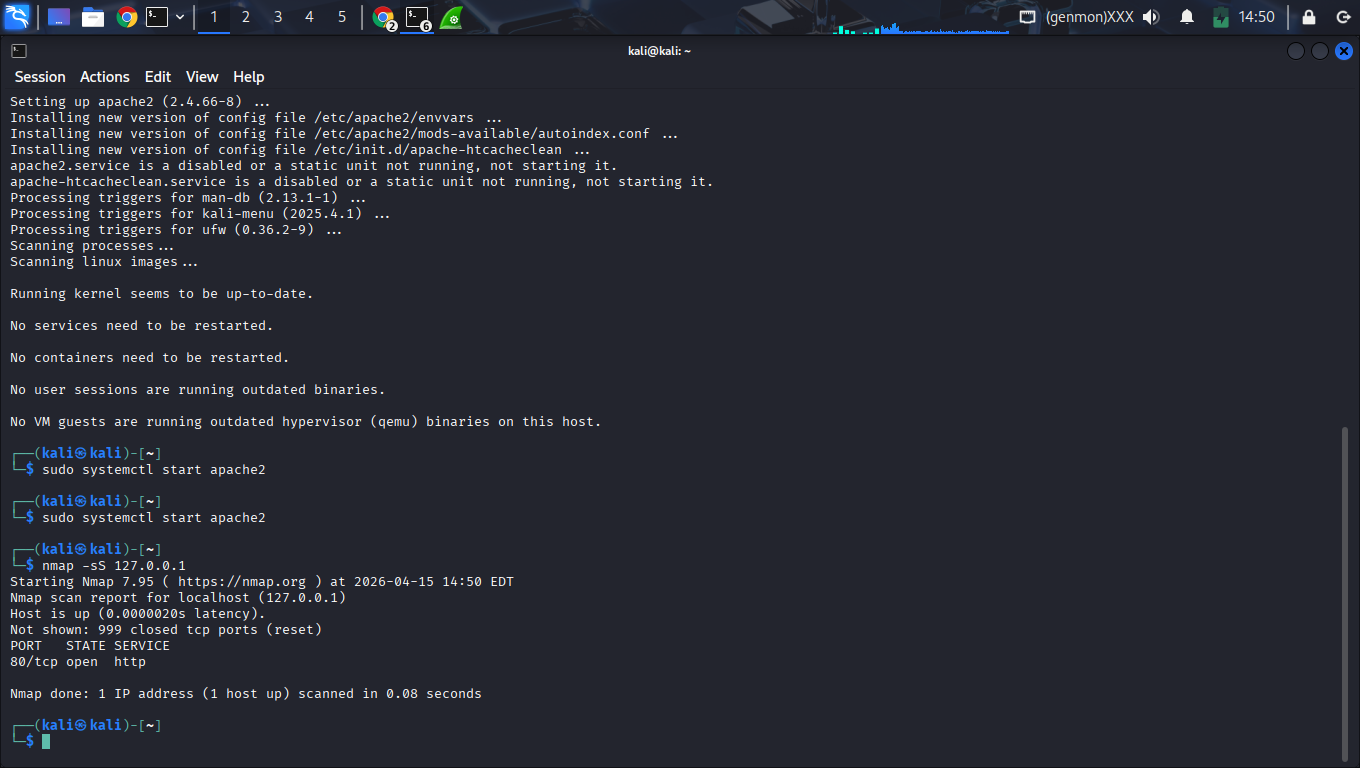
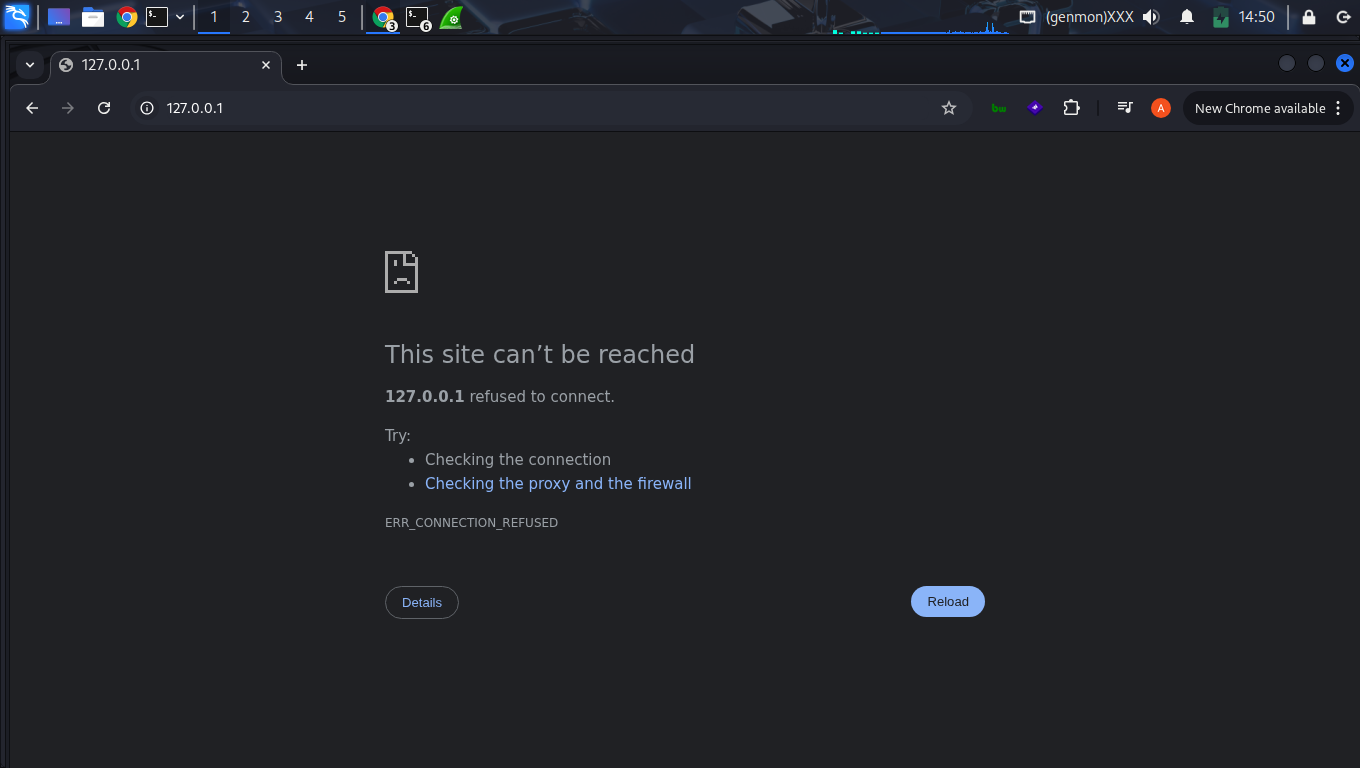
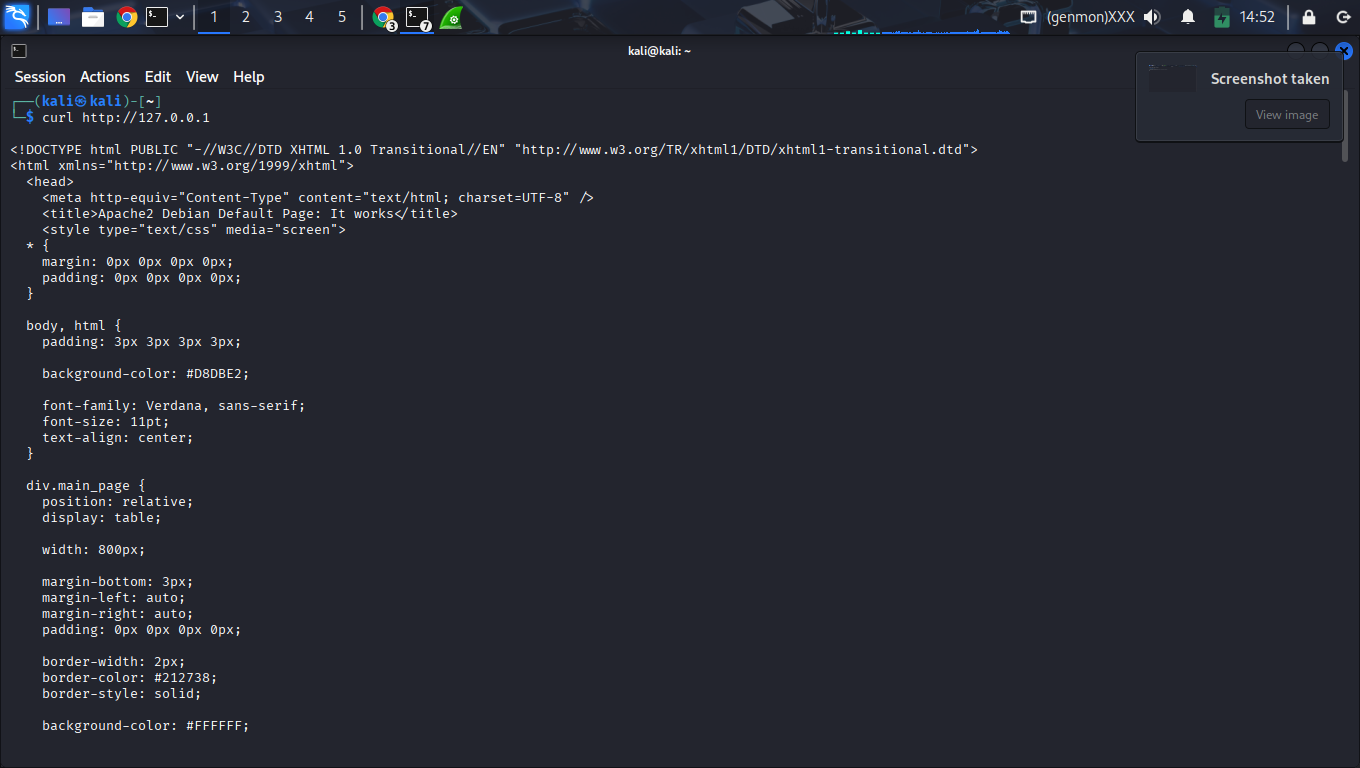
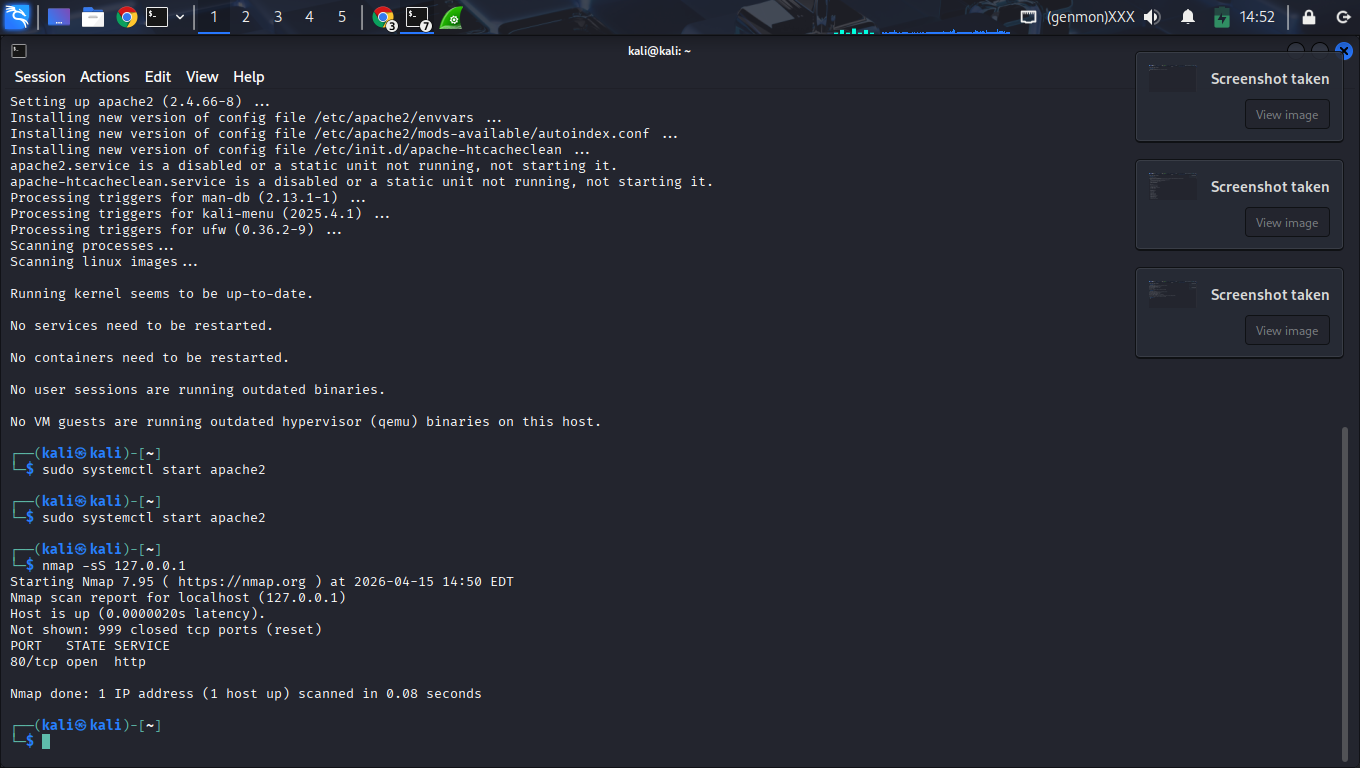
4. Exposure: Local Service Discovery
Medium SeverityPort 80 (Apache)
Successful transport-layer connection to 127.0.0.1 detected. Service is fully interactive.
Risk Assessment
Active services expand the local attack surface and should be hardened to prevent exploitation.
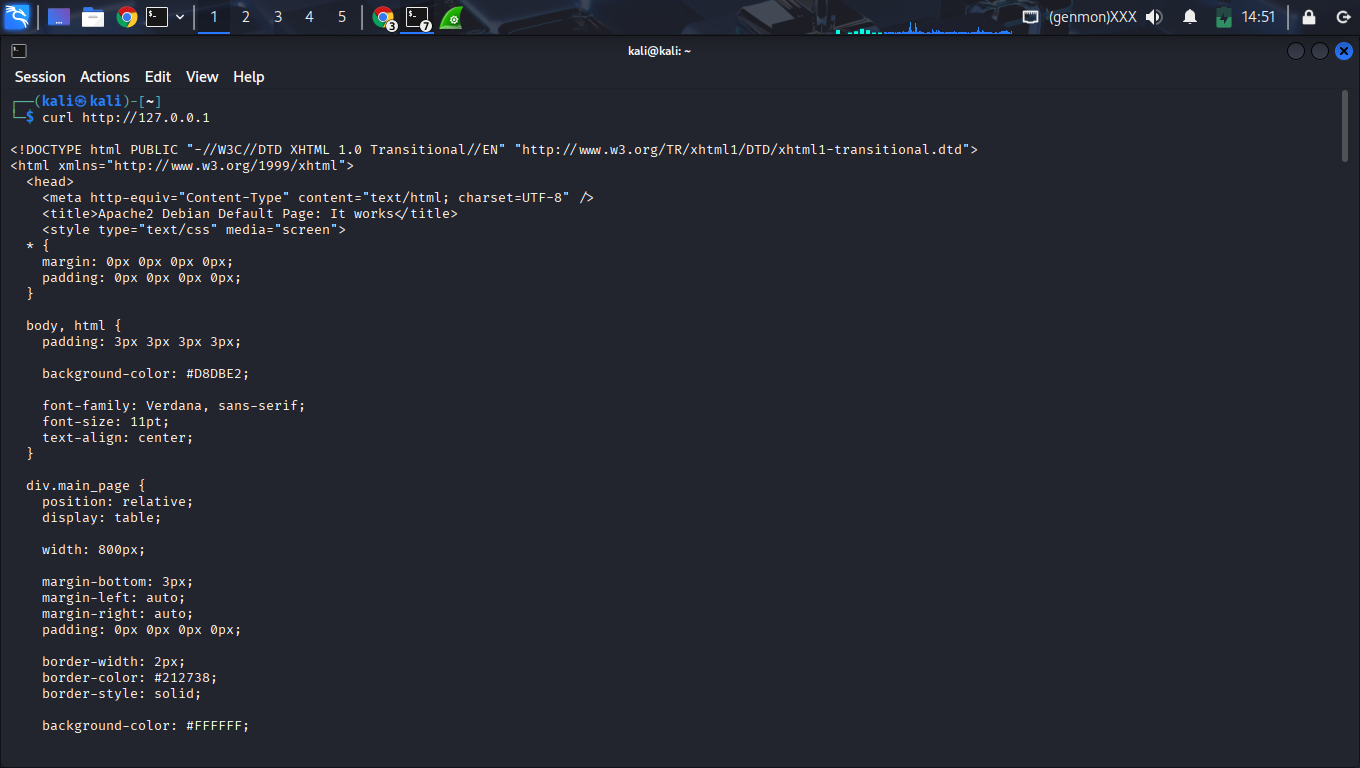
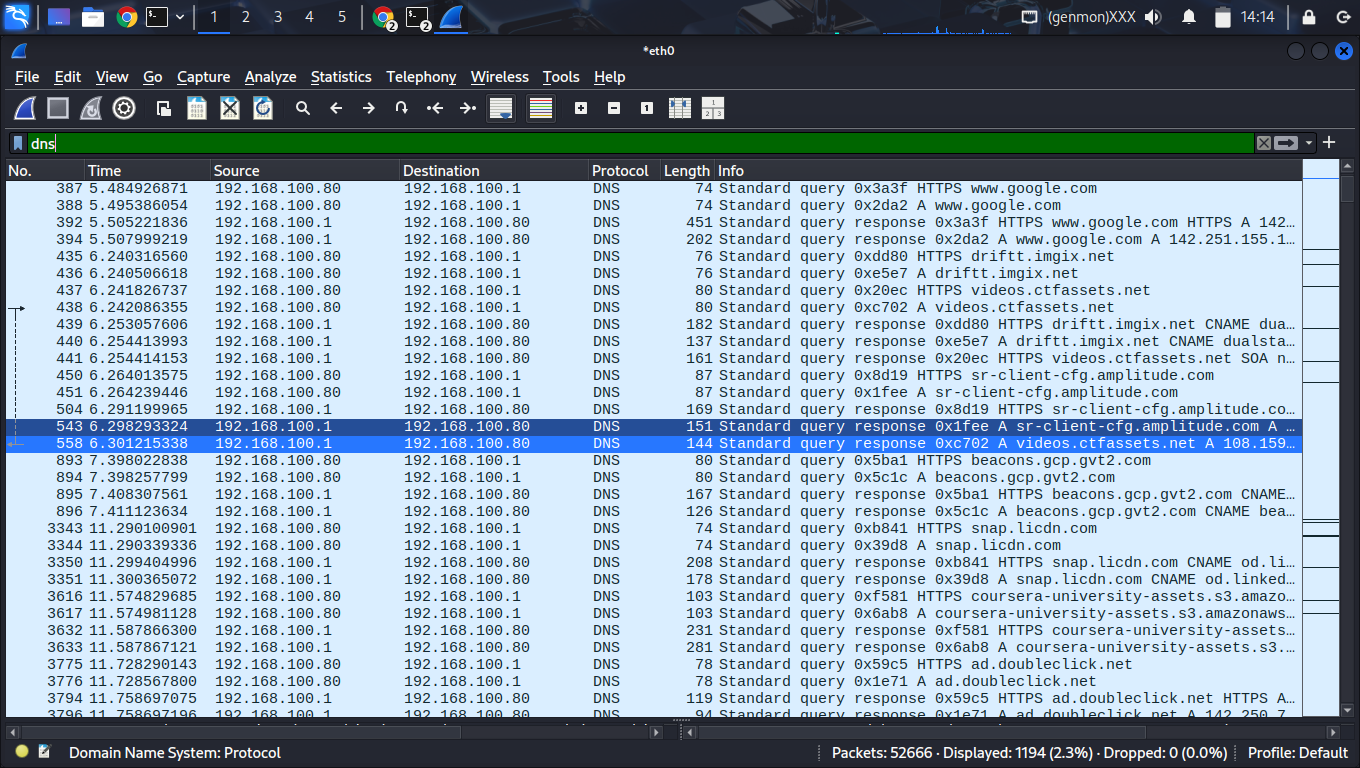
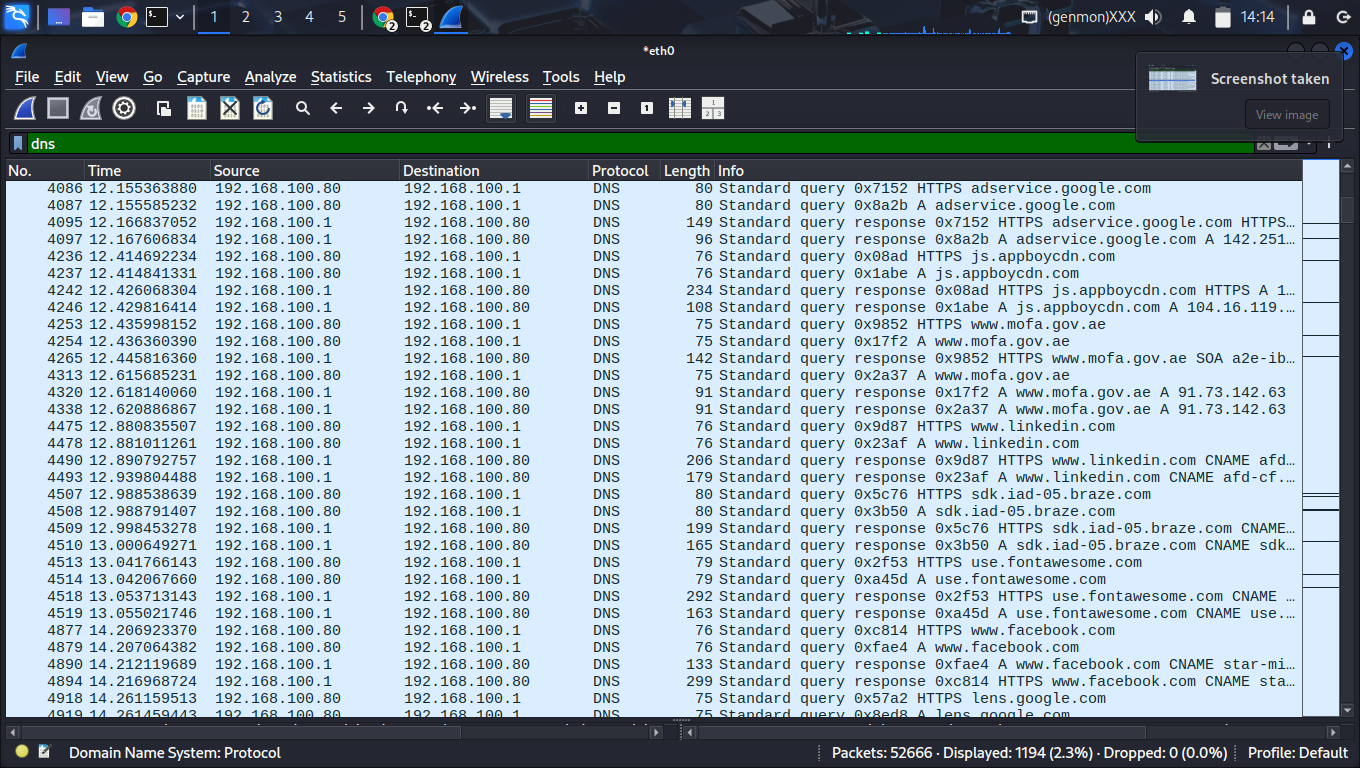
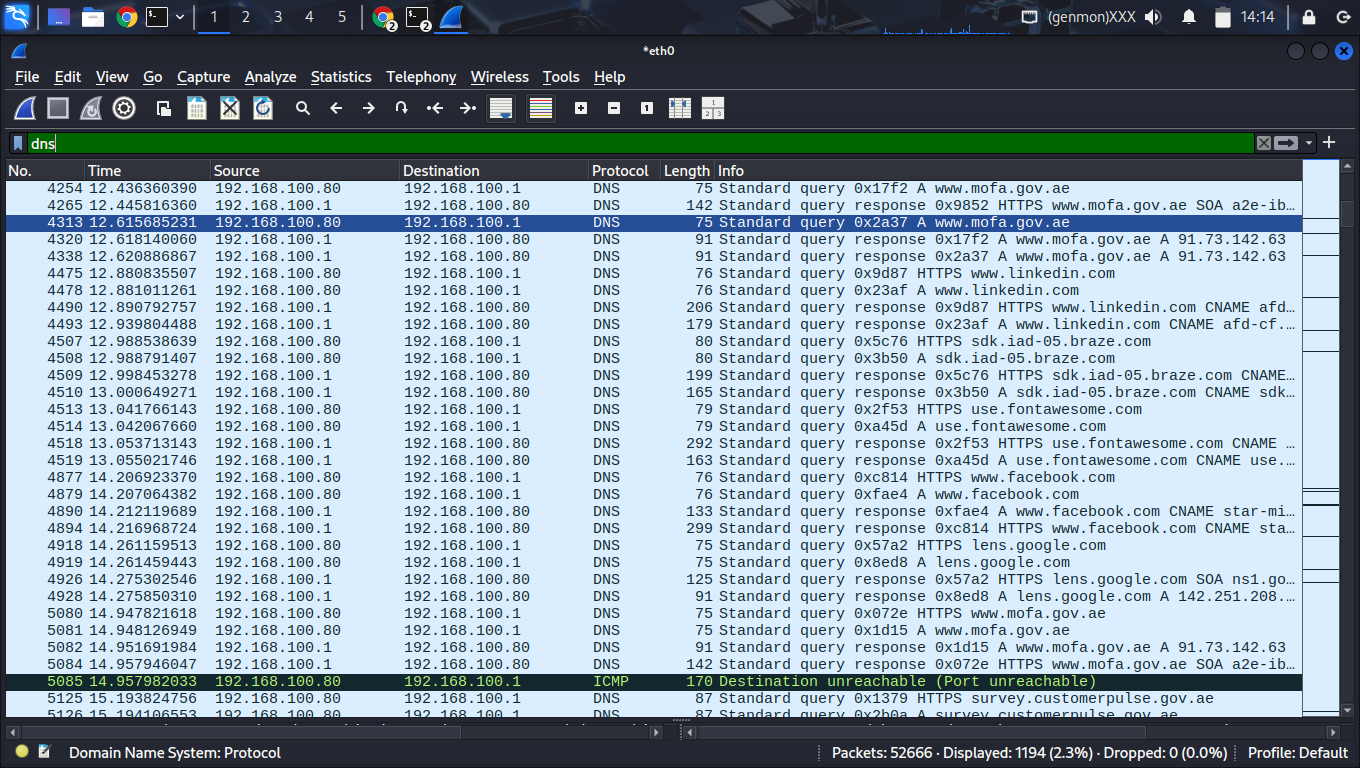
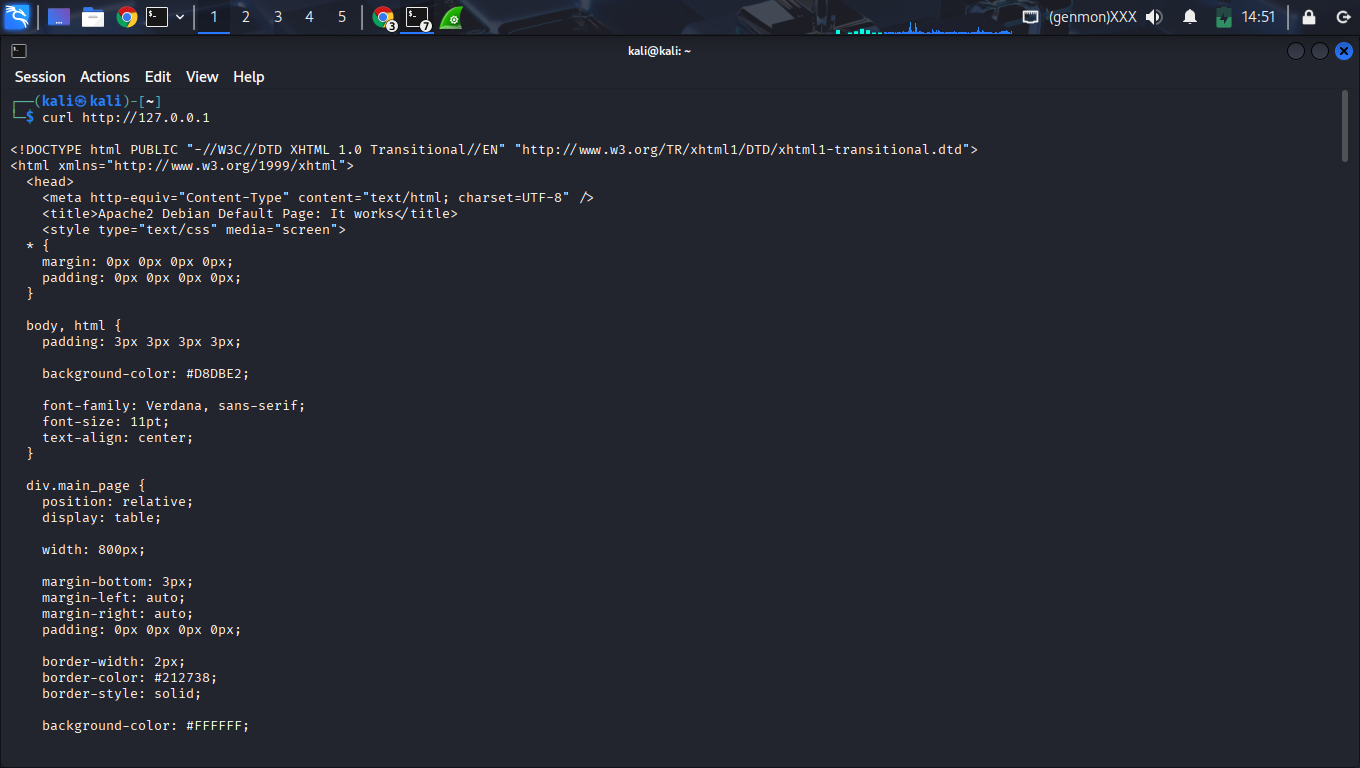
5. Vulnerability: Cleartext Traffic
High SeverityPlaintext HTTP traffic captured. All application-layer headers and content are visible to passive monitoring tools on the network.
6. SOC Analysis Mapping
| Phase | Evidence Observed | Mapped Technique |
|---|---|---|
| Scanning | Massive SYN packet burst | T1046 (Network Scanning) |
| Enumeration | Targeted HTTP connection | T1016 (Device Discovery) |
| Exfiltration Risk | Plaintext HTTP GET requests | T1041 (Exfiltration) |
7. Visual Evidence Appendix
Recommendations
- Enforce transport security with TLS/HTTPS.
- Monitor network logs for abnormal SYN packet rates.
- Update firewall to log and alert on dropped recon probes.
- Restrict access to local management/dev services.