The Architecture
Environment & Tools
- OS: Kali Linux (VMware)
- Language: Python 3 (Scapy, Requests)
- Interface: lo (Loopback)
- Simulation: hping3 (SYN/UDP/Flood)
Config Thresholds
| Time Window | 5 Seconds |
| SYN Threshold | 100 packets |
| UDP Threshold | 200 packets |
| Cooldown | 5 Seconds |
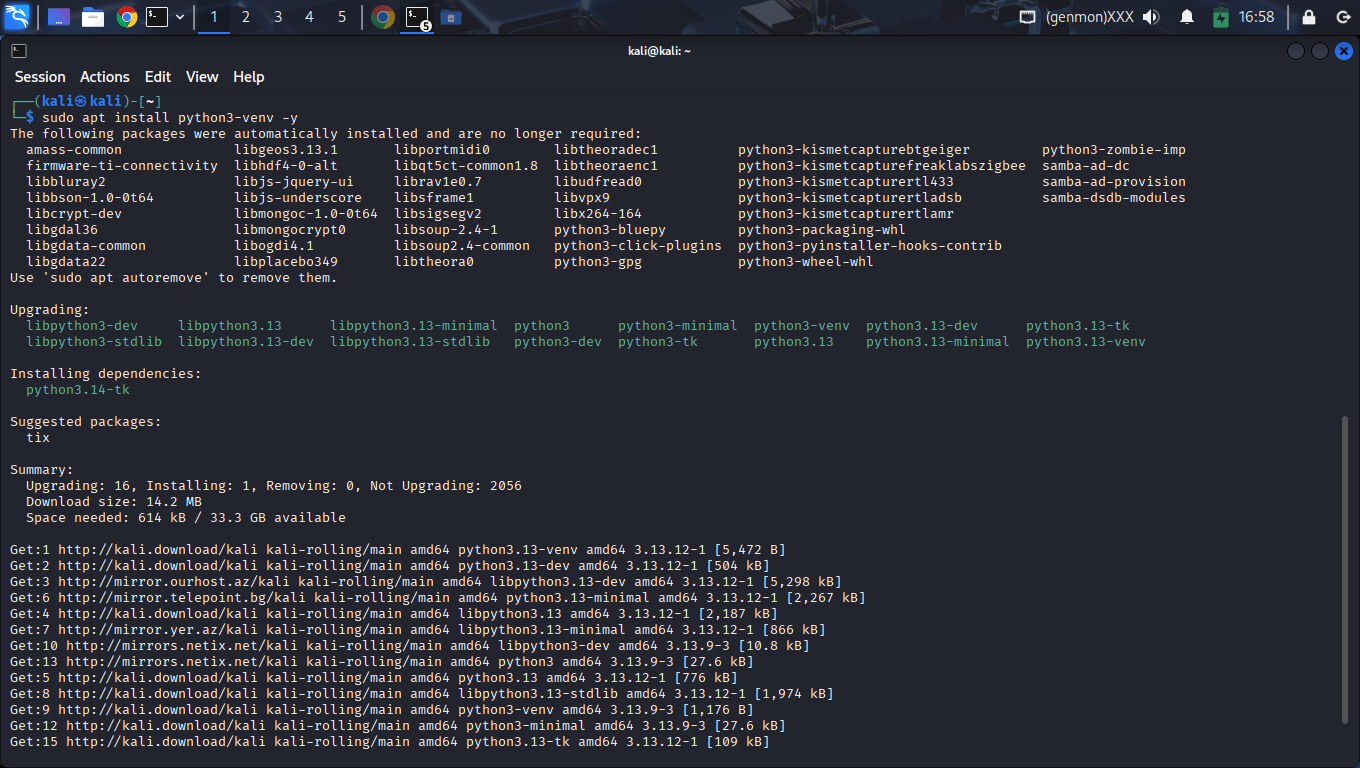
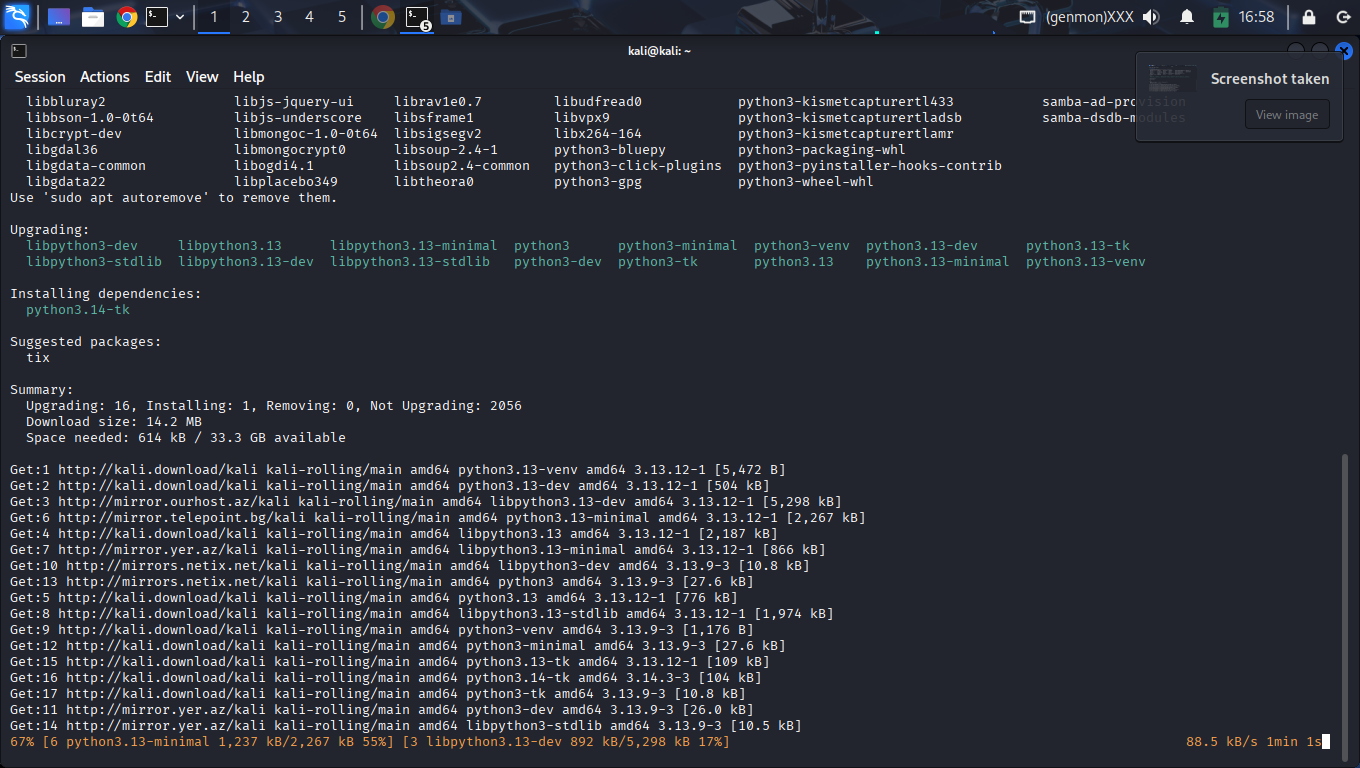
Foundations & Setup
The initialization sequence required to prepare the Kali Linux environment for real-time packet processing.
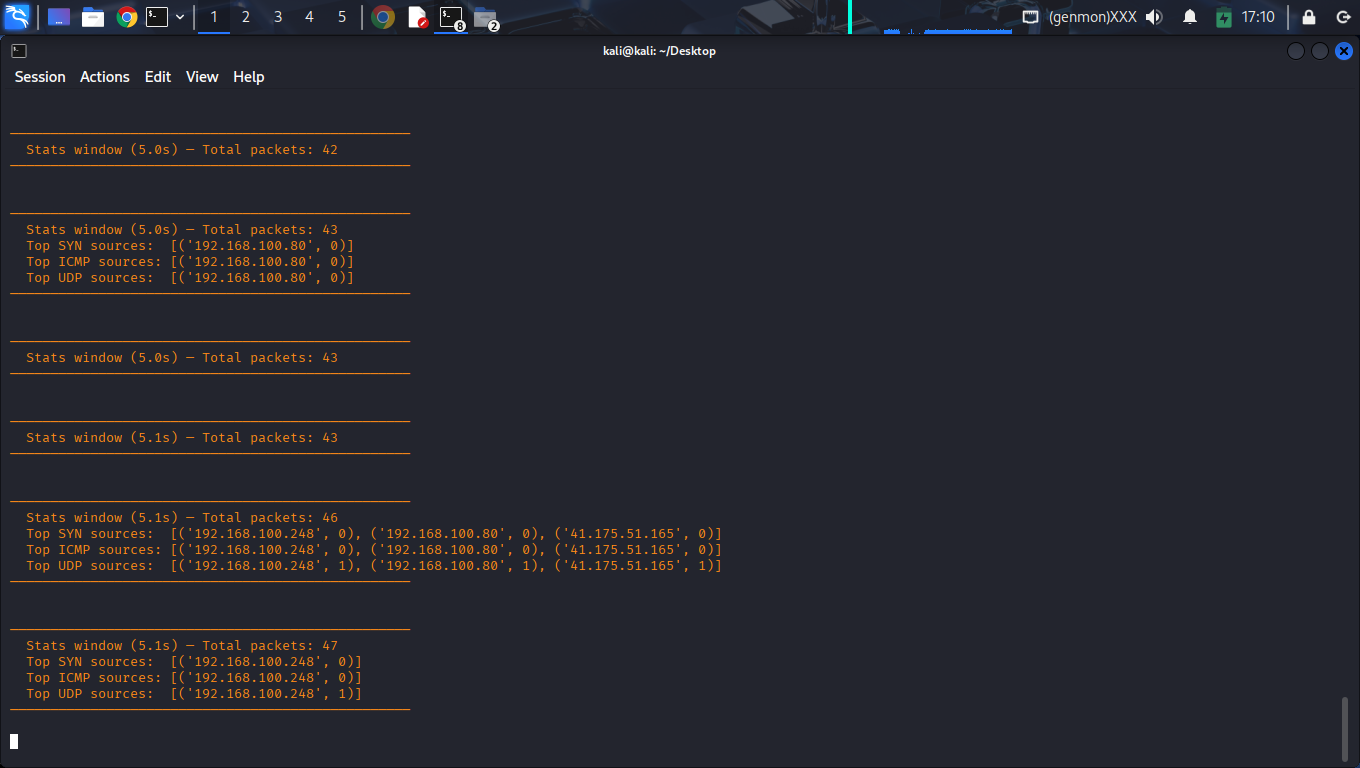
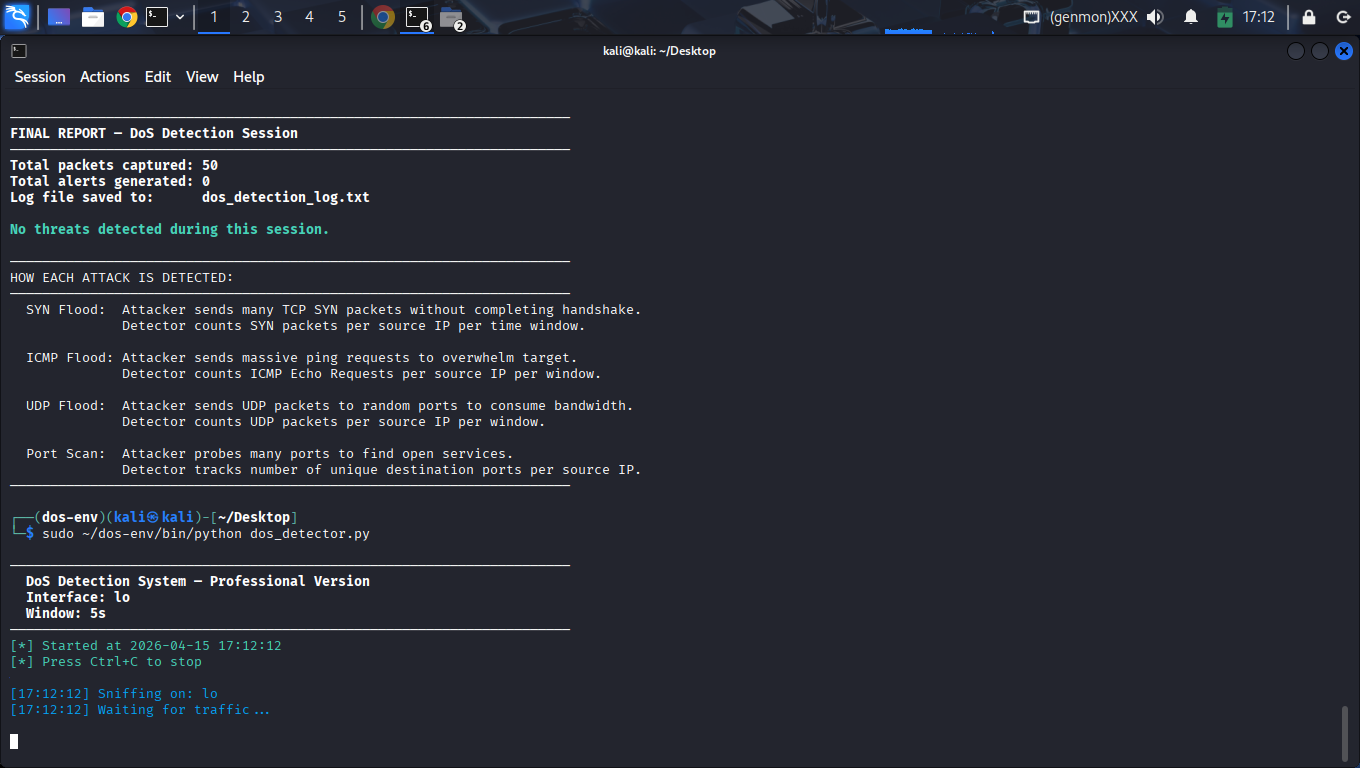
Valid Terminal Flow
Complete end-to-end trace from system startup to final analytics generation.
4-Stage Attack Simulation Lifecycle
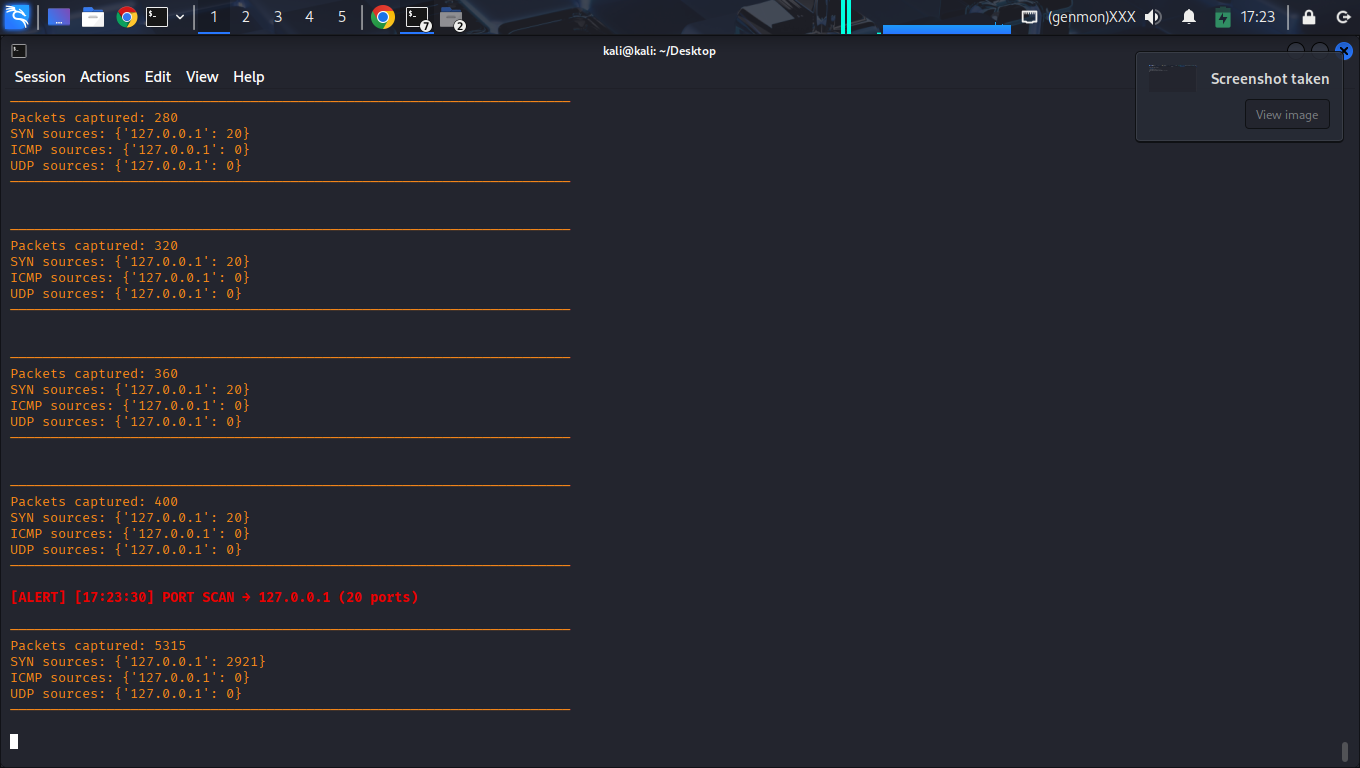
Detector initialized on lo. Captured 11,204 packets of background noise. No false positives observed during baseline conditions.
Command: No dedicated scanning tool was used
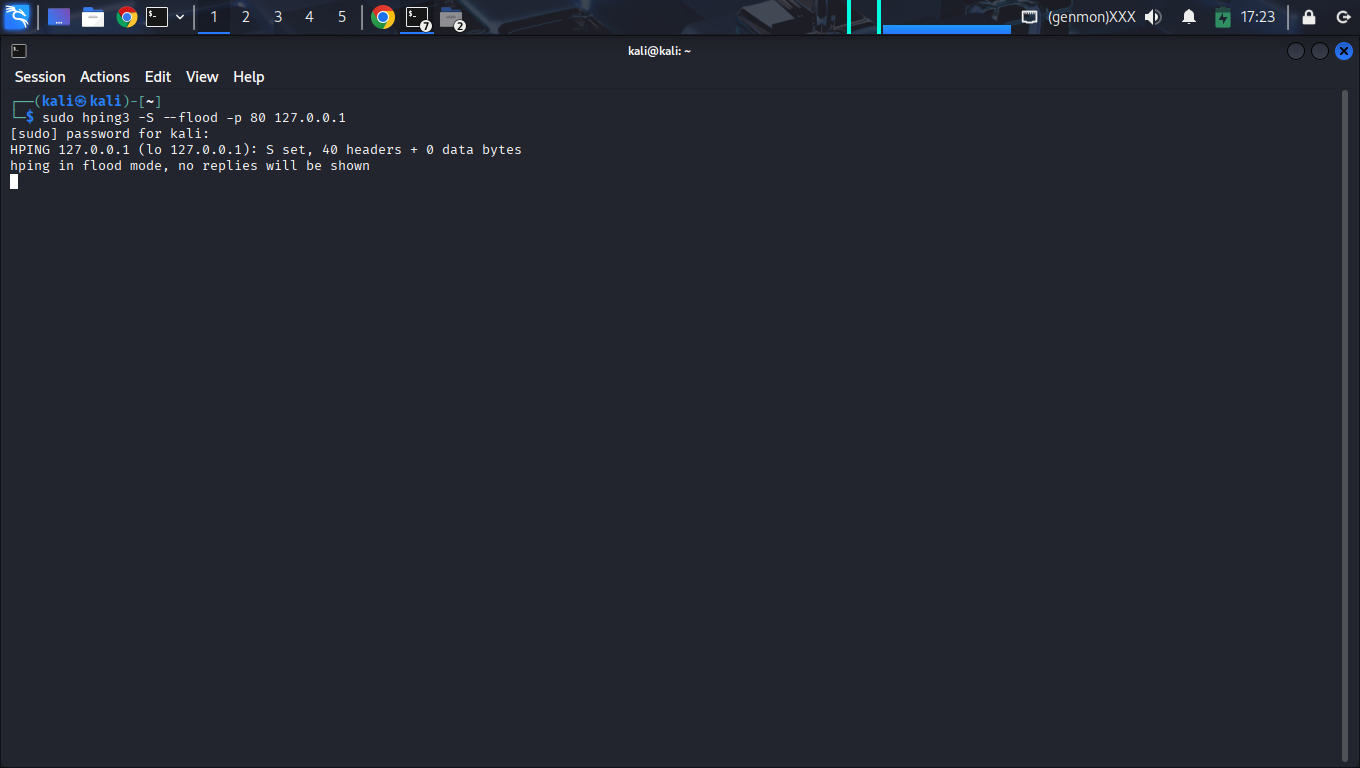
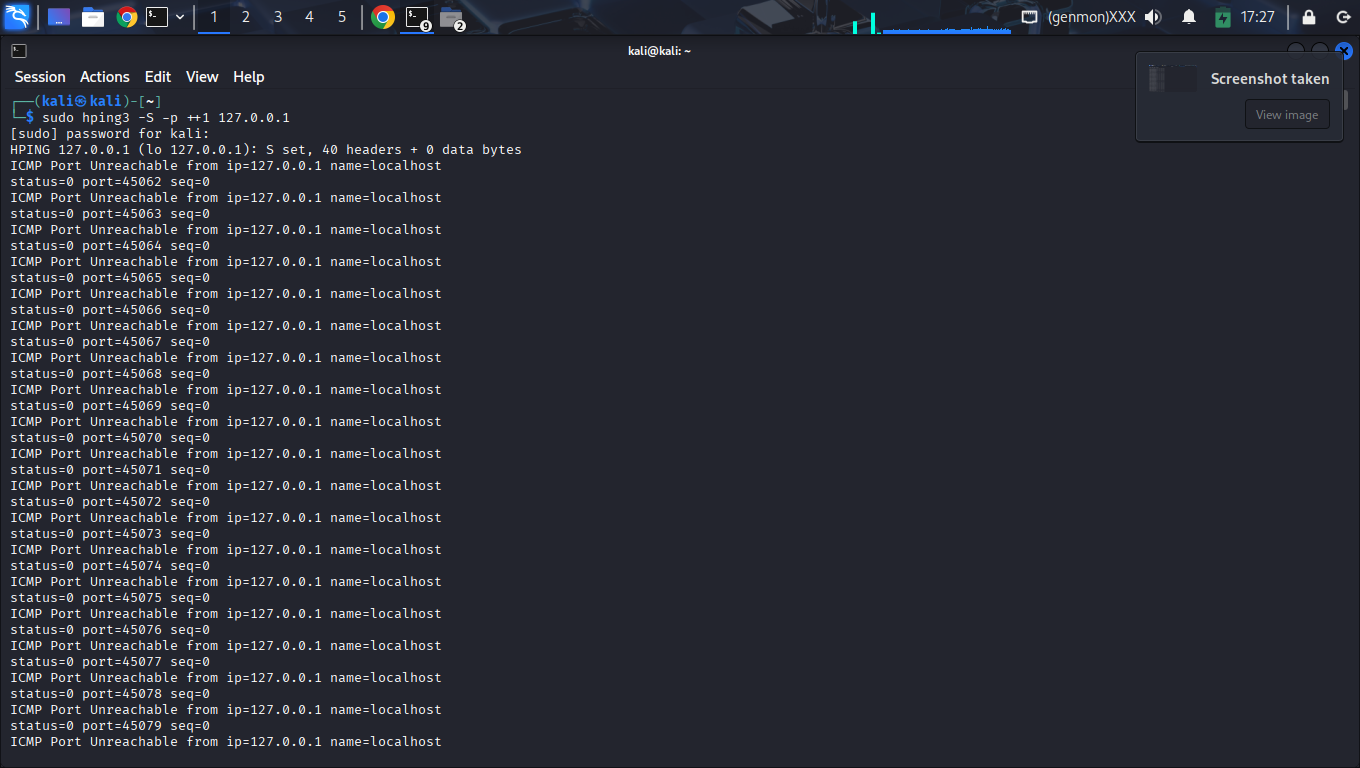
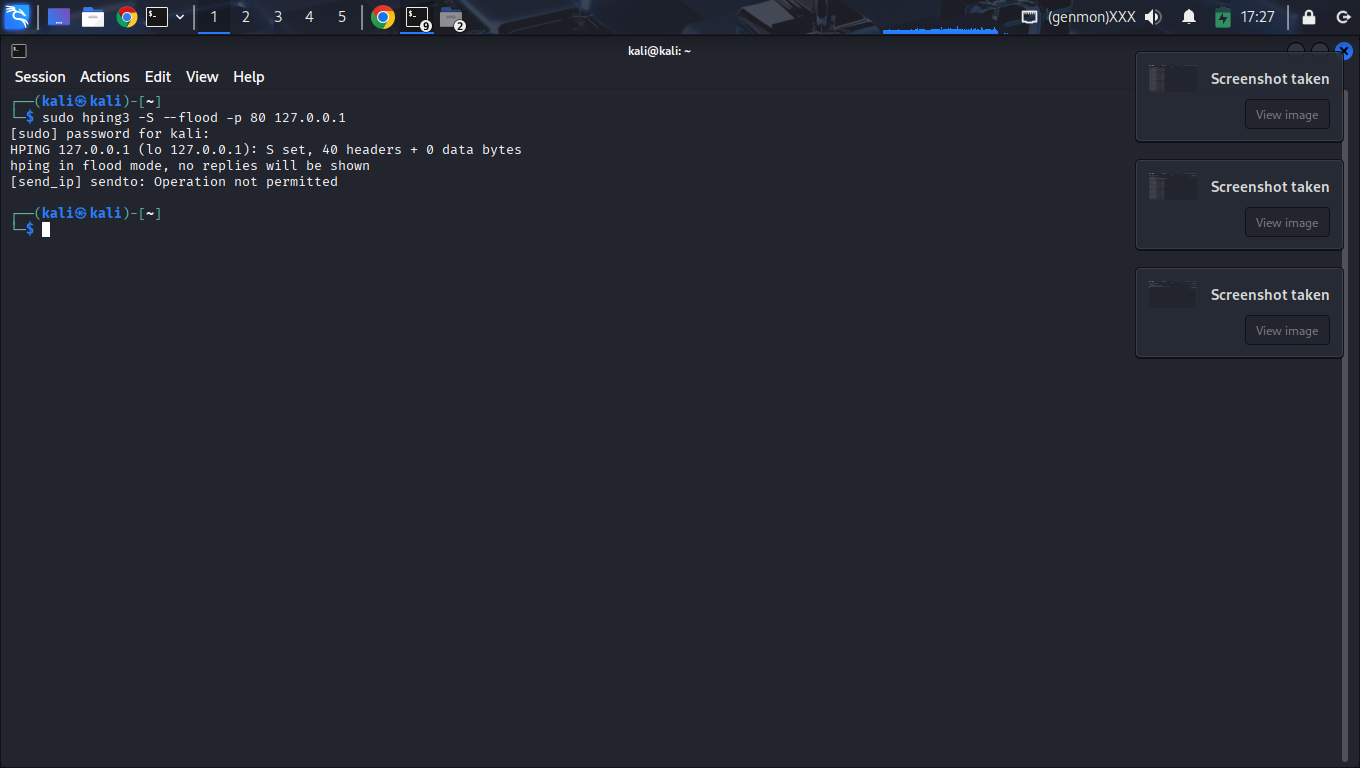
Trigger Source: High-rate traffic generated using:sudo hping3 -S --flood -p 80 127.0.0.1
Result: PORT SCAN alert was triggered due to heuristic detection logic.
Explanation: The detection system flagged port scanning behavior based on:
- High packet rate
- Rapid interaction patterns
- Multiple port observations within the time window
This behavior highlights the potential for false positives in threshold-based intrusion detection systems when exposed to high-rate traffic patterns.
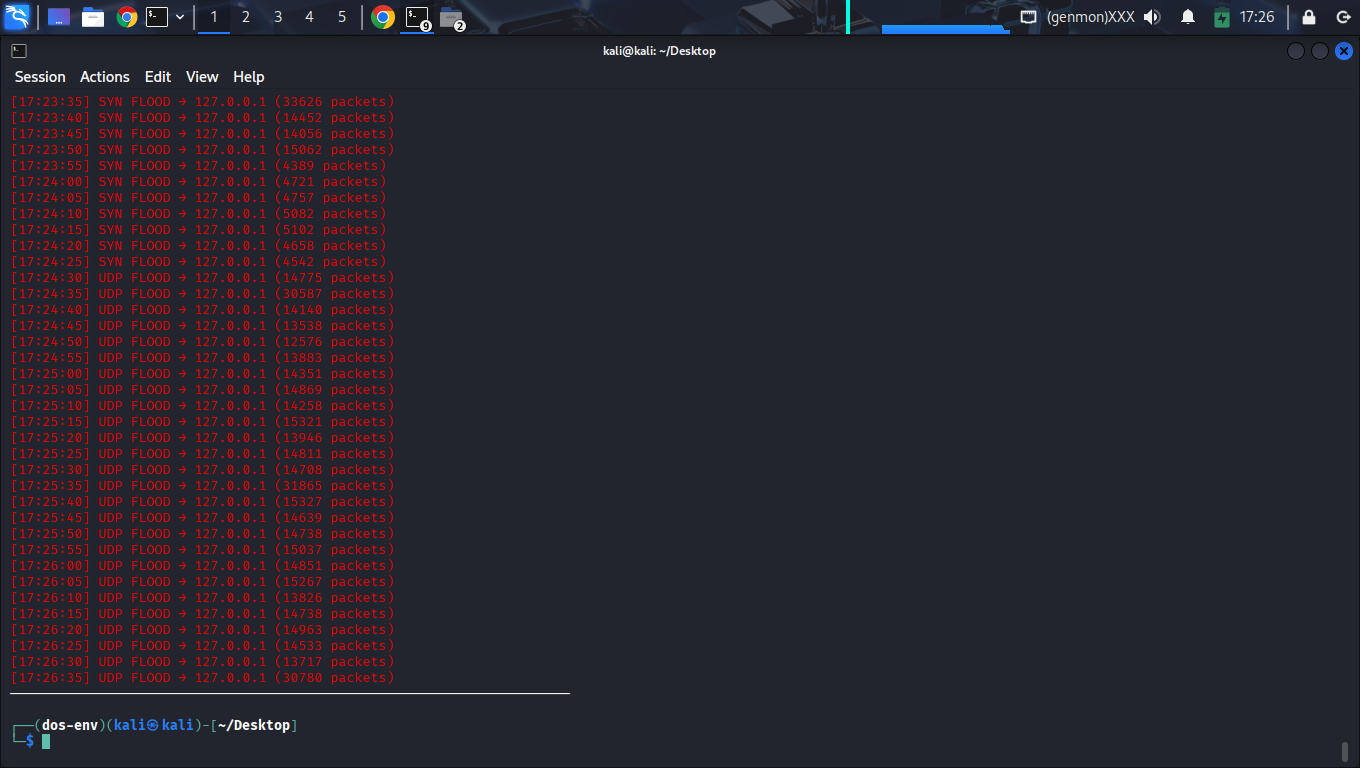
Command: sudo hping3 -S --flood -p 80 127.0.0.1
Result: 33,626 SYN packets detected per window. Real-time detection observed within the 5-second detection window.
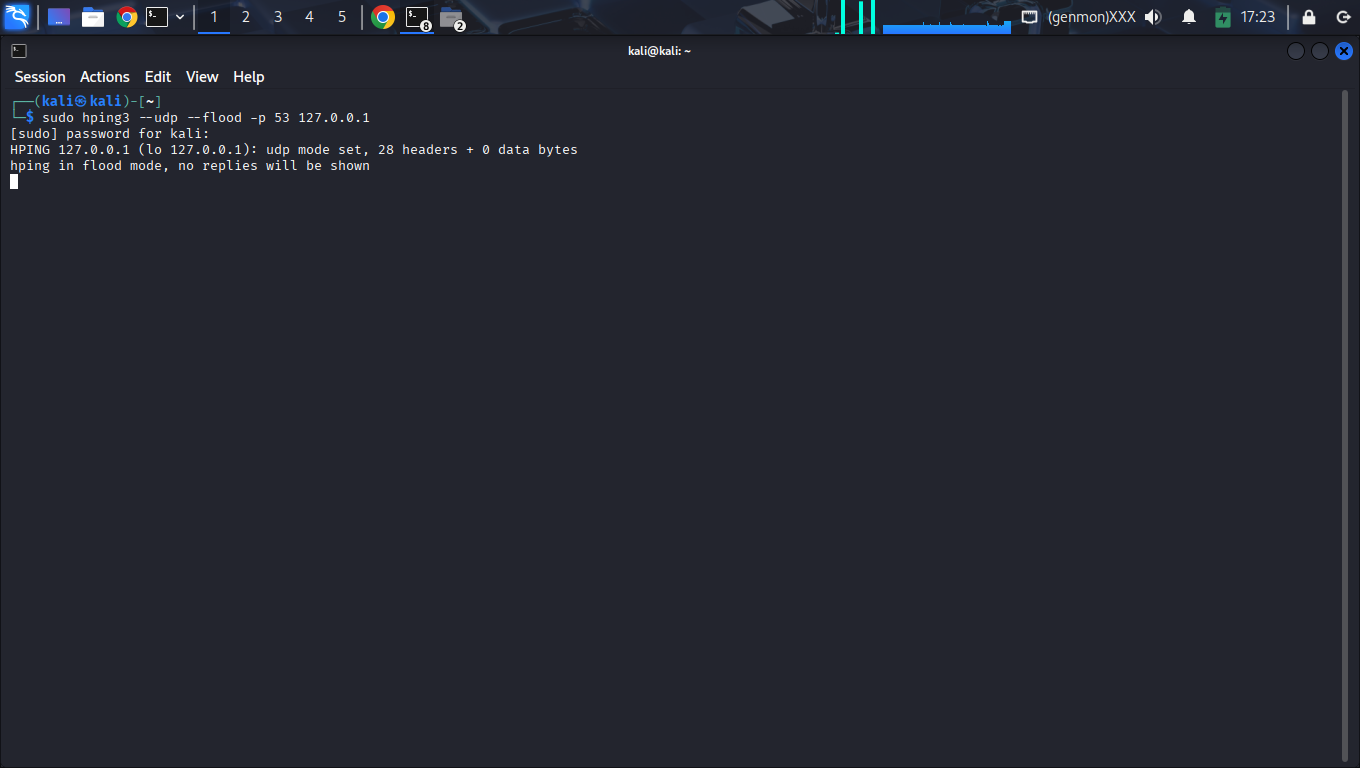
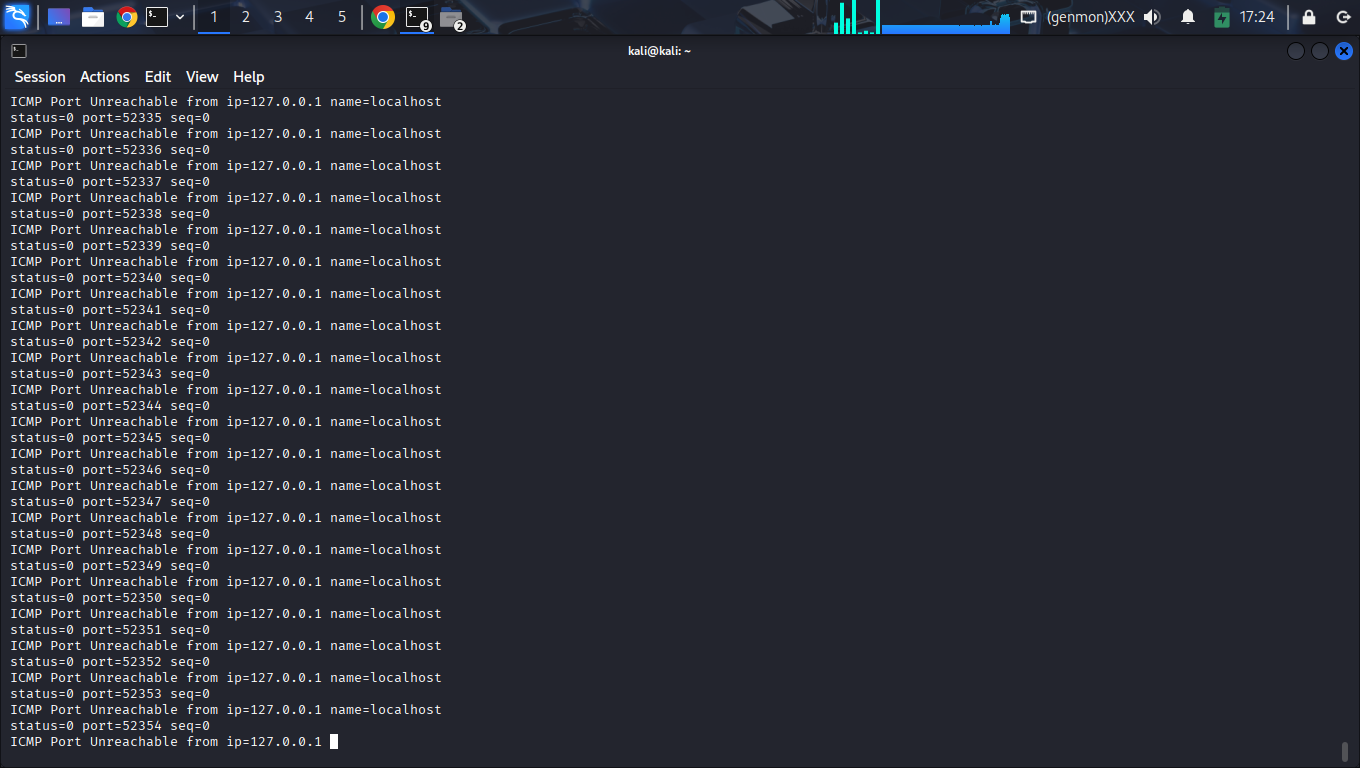
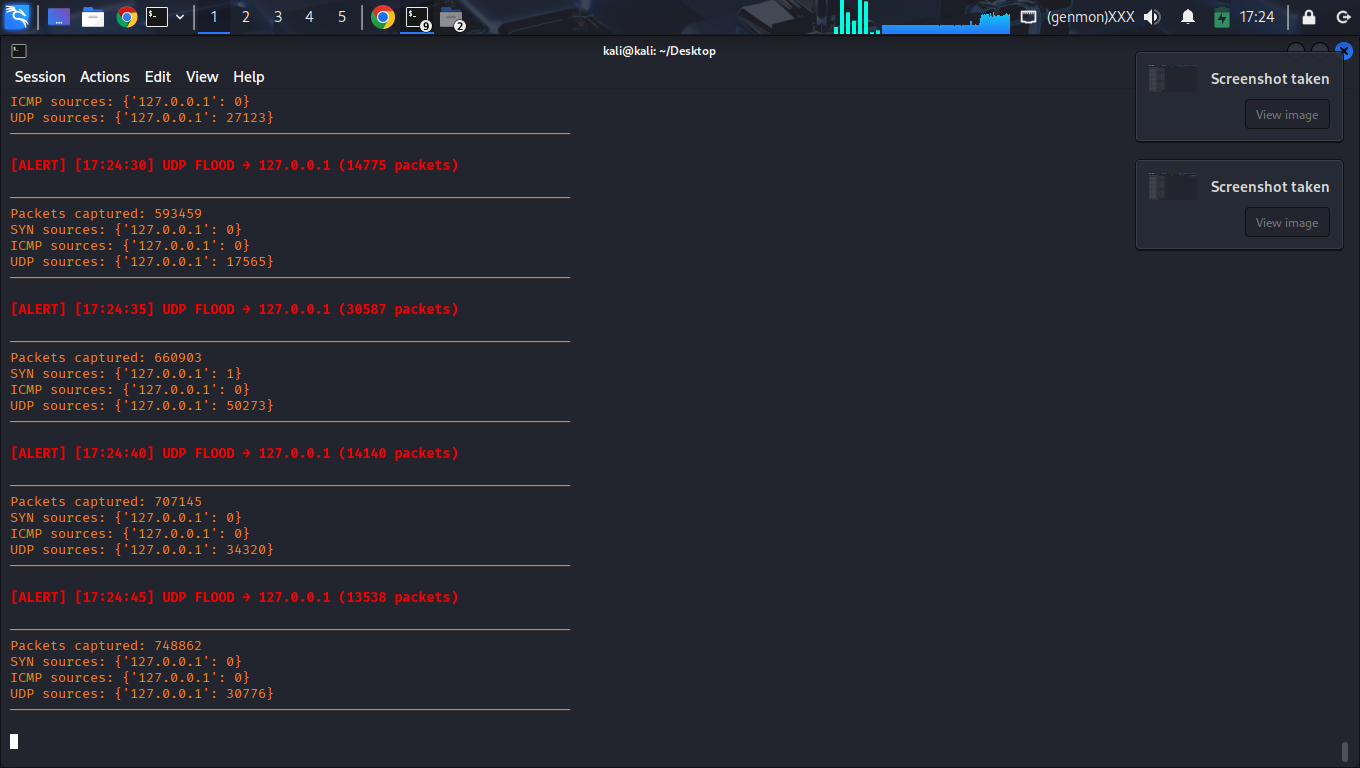
Command: sudo hping3 --udp --flood -p 53 127.0.0.1
Result: Successfully detected bandwidth saturation + ICMP "Port Unreachable" side-channel confirmation signals.
Curated Forensic Evidence Registry
A strictly curated sequence of 18 unique forensic captures documenting the complete lifecycle—zero duplicates, 100% technical relevance.
Step 1: Environment & Dependency Provisioning
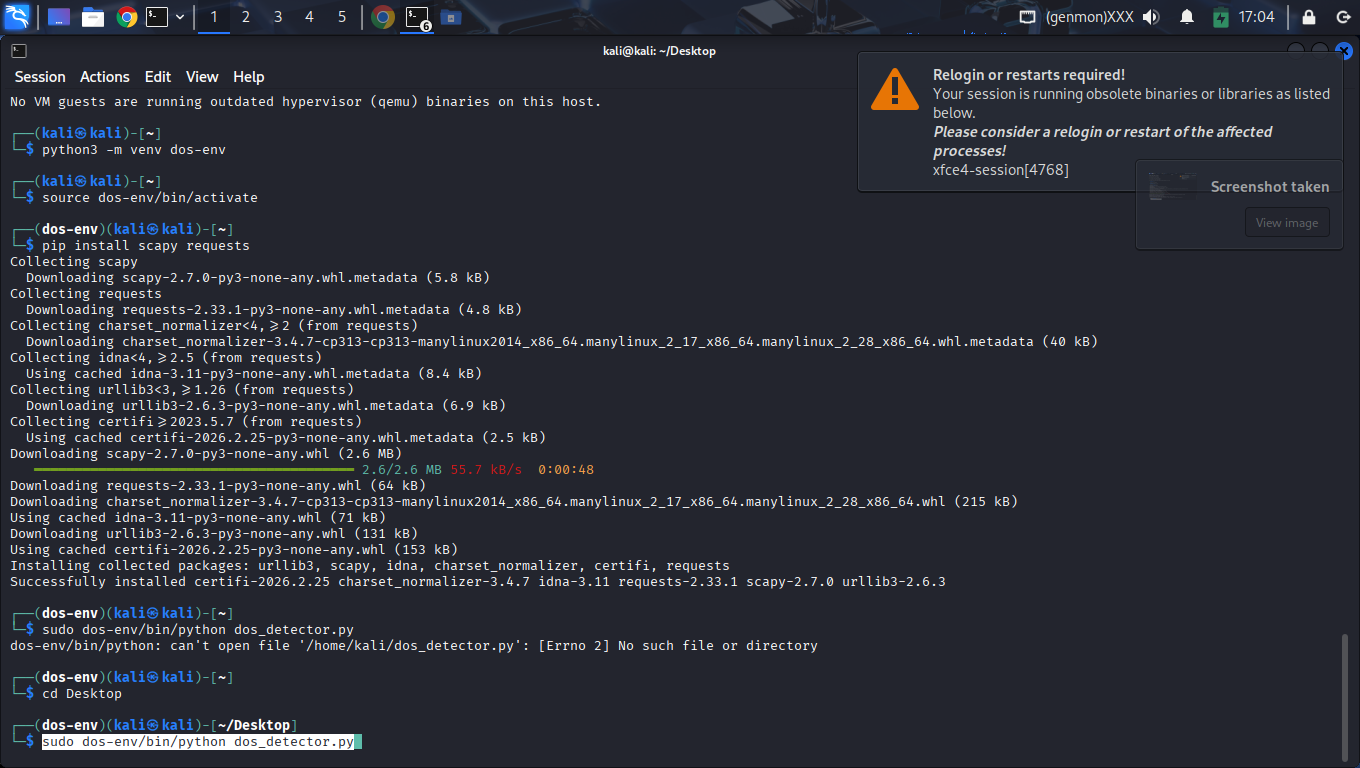
Step 2: Engine Boot & Sniffer Binding
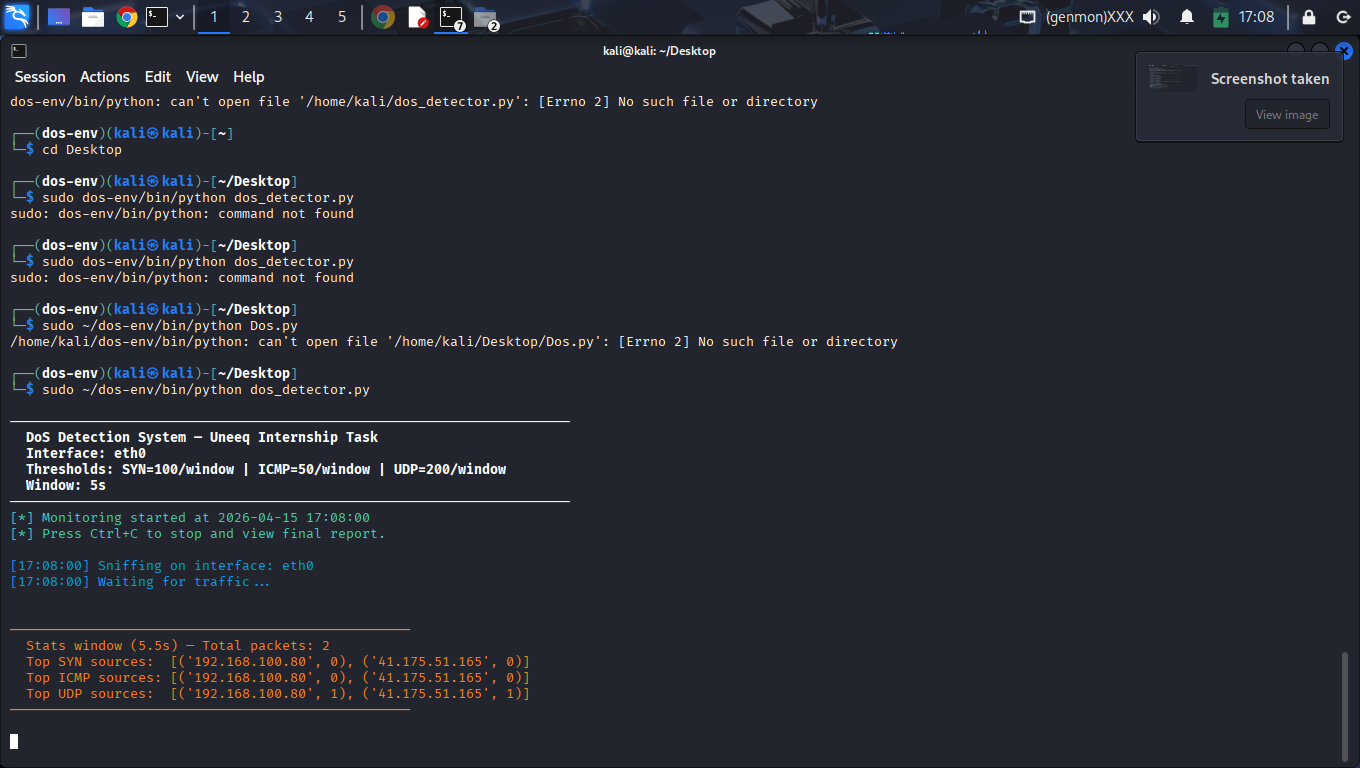
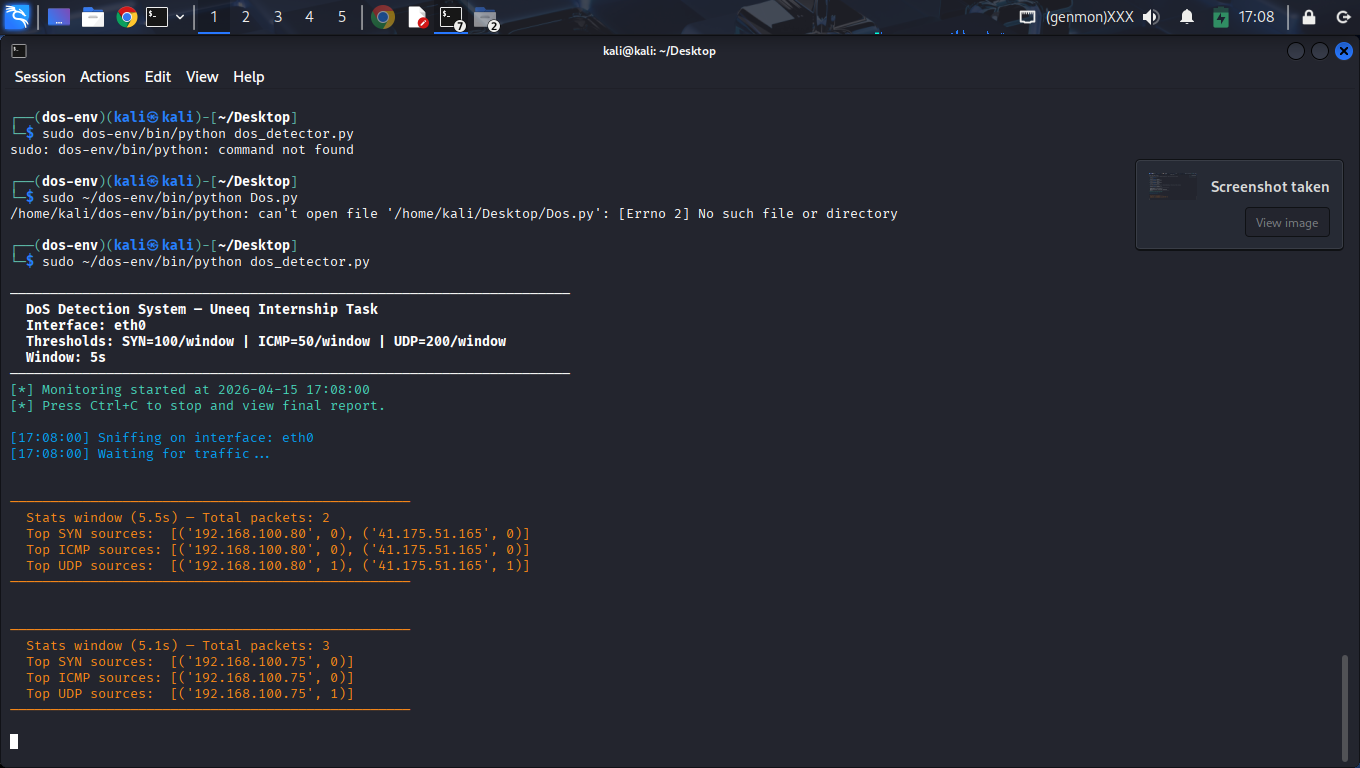
Step 3: Traffic Baselining
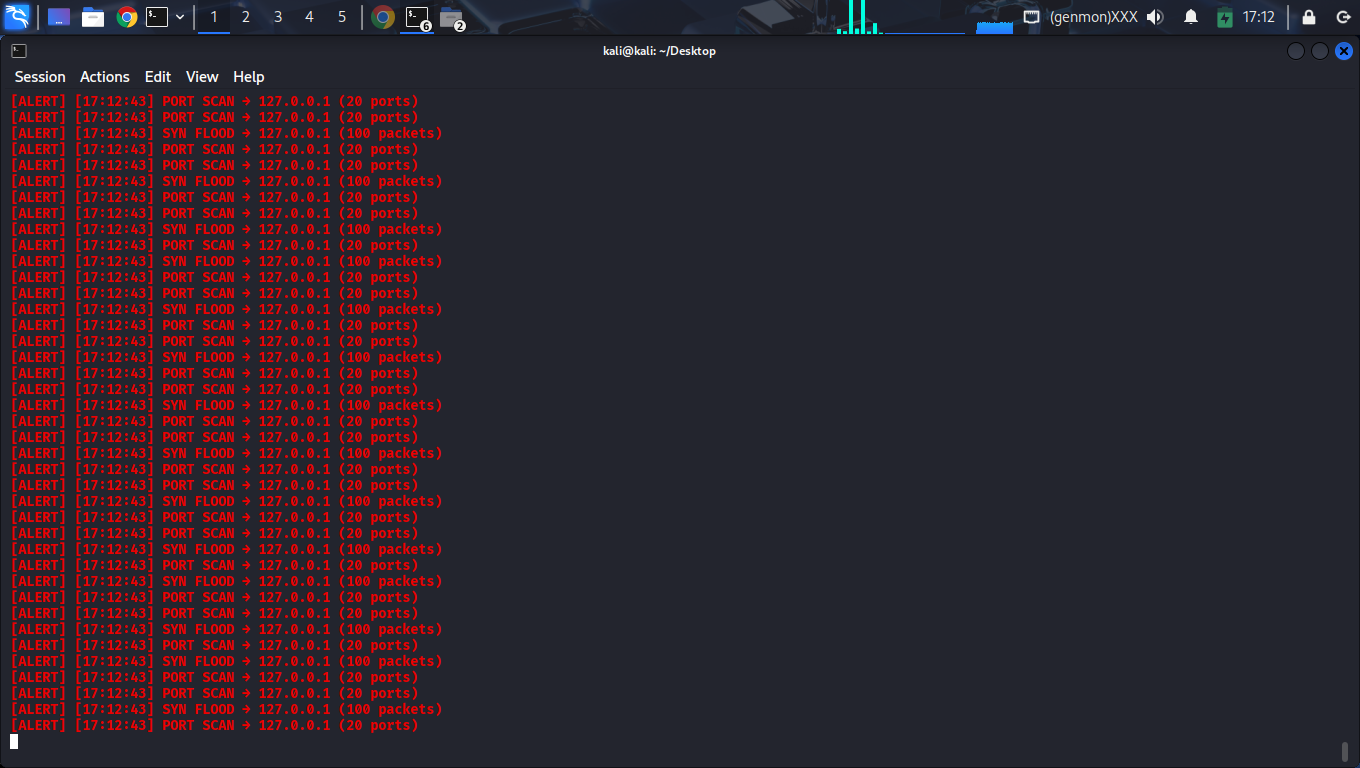
Step 4: TCP SYN & Mapping Detection
Step 5: Volumetric UDP & Host Impact
Step 6: Graceful Termination & Audit
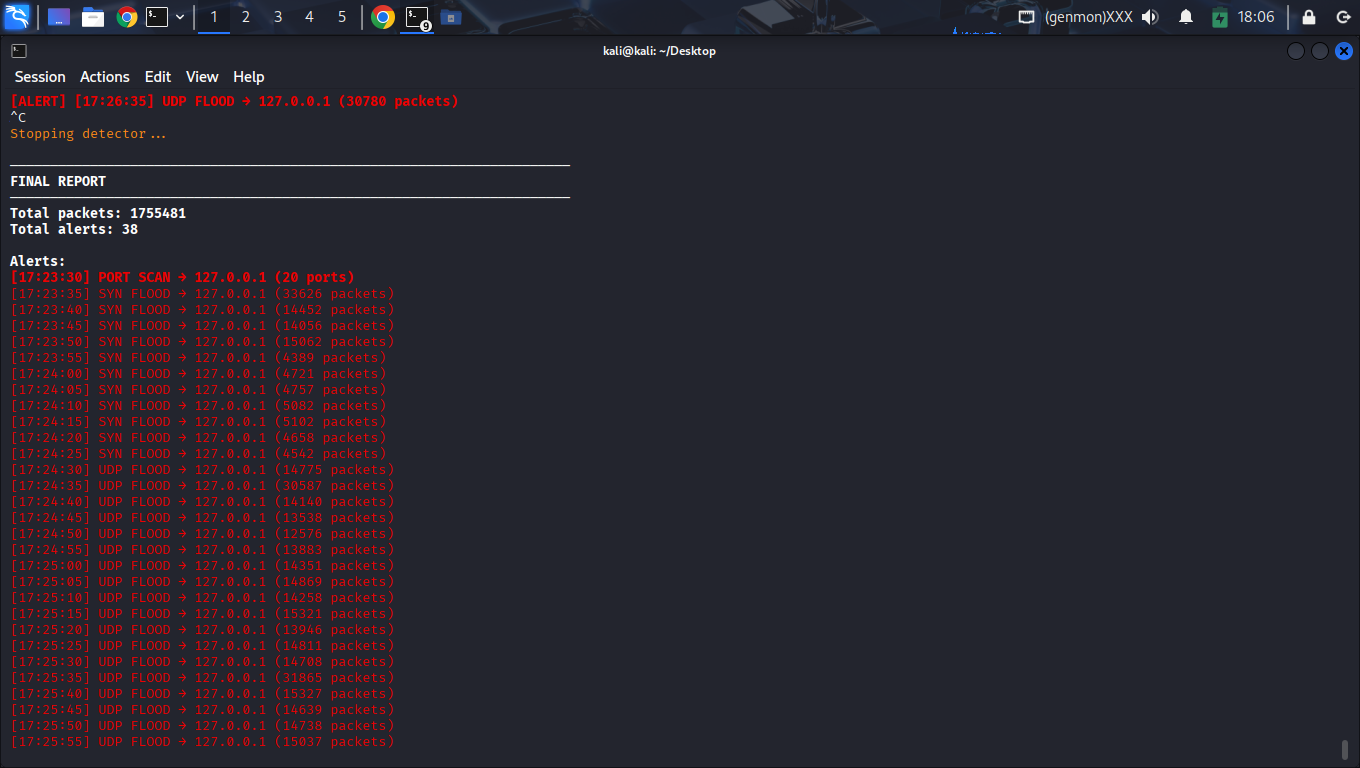
Reliability Metrics
The detector proved resilient under synthetic extreme load scenarios.
Multi-Vector Detection
(TCP / UDP / ICMP / Scan)
Comprehensive Coverage0
System Crashes
Stable real-time packet processing38
Alerts Logged
Verified unique eventsComplete Source Code
The functional Python script used for real-time packet analysis and multi-vector detection.
#!/usr/bin/env python3
"""
DoS Detection System - Alert Cooldown Enabled
Author: Youssef Moataz
"""
import sys
import time
import signal
from collections import defaultdict
from datetime import datetime
from scapy.all import sniff, IP, TCP, ICMP, UDP
# Config
INTERFACE = "lo"
TIME_WINDOW = 5
SYN_THRESHOLD = 100
ICMP_THRESHOLD = 50
UDP_THRESHOLD = 200
PORT_SCAN_THRESHOLD = 20
ALERT_COOLDOWN = 5
LOG_FILE = "dos_detection_log.txt"
# State Tracking
syn_count = defaultdict(int)
icmp_count = defaultdict(int)
udp_count = defaultdict(int)
port_targets = defaultdict(set)
last_alert_time = defaultdict(float)
total_packets = 0
alert_log = []
window_start = time.time()
# Logging
def log_alert(message):
timestamp = datetime.now().strftime('%H:%M:%S')
msg = f"[{timestamp}] [ALERT] {message}"
print(msg)
alert_log.append(msg)
with open(LOG_FILE, "a") as f:
f.write(msg + "\n")
def reset_counters():
global window_start
syn_count.clear()
icmp_count.clear()
udp_count.clear()
port_targets.clear()
window_start = time.time()
def check_thresholds(ip):
current_time = time.time()
if syn_count[ip] >= SYN_THRESHOLD and (current_time - last_alert_time[ip] > ALERT_COOLDOWN):
log_alert(f"SYN FLOOD detected from {ip} ({syn_count[ip]} packets)")
last_alert_time[ip] = current_time
if icmp_count[ip] >= ICMP_THRESHOLD and (current_time - last_alert_time[ip] > ALERT_COOLDOWN):
log_alert(f"ICMP FLOOD detected from {ip} ({icmp_count[ip]} packets)")
last_alert_time[ip] = current_time
if udp_count[ip] >= UDP_THRESHOLD and (current_time - last_alert_time[ip] > ALERT_COOLDOWN):
log_alert(f"UDP FLOOD detected from {ip} ({udp_count[ip]} packets)")
last_alert_time[ip] = current_time
if len(port_targets[ip]) >= PORT_SCAN_THRESHOLD and (current_time - last_alert_time[ip] > ALERT_COOLDOWN):
log_alert(f"PORT SCAN detected from {ip} ({len(port_targets[ip])} ports)")
last_alert_time[ip] = current_time
# Packet Handler
def packet_handler(packet):
global total_packets, window_start
if time.time() - window_start >= TIME_WINDOW:
reset_counters()
if not packet.haslayer(IP):
return
total_packets += 1
src = packet[IP].src
if packet.haslayer(TCP):
flags = packet[TCP].flags
if flags & 0x02 and not flags & 0x10:
syn_count[src] += 1
port_targets[src].add(packet[TCP].dport)
elif packet.haslayer(ICMP):
if packet[ICMP].type == 8:
icmp_count[src] += 1
elif packet.haslayer(UDP):
udp_count[src] += 1
port_targets[src].add(packet[UDP].dport)
check_thresholds(src)
def final_report():
print("\n--- FINAL REPORT ---")
print(f"Total packets processed: {total_packets}")
print(f"Total alerts generated: {len(alert_log)}")
print("--------------------")
def stop(sig, frame):
print("\nStopping detector...")
final_report()
sys.exit(0)
def main():
import os
if os.geteuid() != 0:
print("[ERROR] Please run with sudo")
sys.exit(1)
signal.signal(signal.SIGINT, stop)
print(f"[*] Starting Sentinel DoS Monitor on interface {INTERFACE}...")
print(f"[*] Window: {TIME_WINDOW}s | Cooldown: {ALERT_COOLDOWN}s")
print("[*] Press Ctrl+C to stop.\n")
sniff(iface=INTERFACE, prn=packet_handler, store=False)
if __name__ == "__main__":
main()